Stormous Ransomware added Cameron Memorial Community Hospital in Indiana to their leak site today and posted a pointer to it on their Telegram channel.

Then they appeared to regret their actions, posting the following only minutes later:
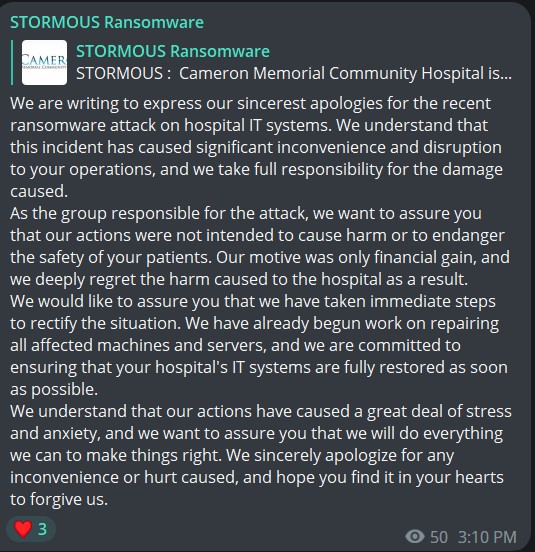
We are writing to express our sincerest apologies for the recent ransomware attack on hospital IT systems. We understand that this incident has caused significant inconvenience and disruption to your operations, and we take full responsibility for the damage caused.
As the group responsible for the attack, we want to assure you that our actions were not intended to cause harm or to endanger the safety of your patients. Our motive was only financial gain, and we deeply regret the harm caused to the hospital as a result.
We would like to assure you that we have taken immediate steps to rectify the situation. We have already begun work on repairing all affected machines and servers, and we are committed to ensuring that your hospital’s IT systems are fully restored as soon as possible.
We understand that our actions have caused a great deal of stress and anxiety, and we want to assure you that we will do everything we can to make things right. We sincerely apologize for any inconvenience or hurt caused, and hope you find it in your hearts to forgive us.
There is no notice or any sign of disrupted services on Cameron’s website at the time of this posting. A query sent asking if them if they had been hit by Stormous ransomware and if Stormous was now trying to undo what they had done did not receive an immediate reply.
Update1, April 4: No reply from the hospital as yet. DataBreaches contacted Stormous and asked for proof that they actually attacked the hospital. They did not provide any, although they did reply to the request. After some back and forth in Tox, they stopped responding, it seems.
So… is Stormous Ransomware for real or are they a scam group as Kela suggested last year? If they are for real, then they did not help themselves by declining to provide some proof of claims.