On May 24, the Vascular Center of Intervention (VCI) in California submitted a breach notification to California and posted a substitute notice on VCI’s website.
The notification, signed by Dr. James Lee, states that on March 29, VCI became aware of unusual activity on its network. An investigation revealed that some patient-related files had been accessed or exfiltrated between February 25 and March 29. The letter notes that the types of information involved might include one or more of the following for any affected patient: medical history, mental or physical condition, medical treatment or diagnosis by a healthcare professional, date of birth, health insurance information, Social Security Number, and Driver’s license information.
A substitute notice on VCI’s website provides essentially the same information but does not mention that affected patients are being offered 12 months of credit monitoring and identity theft protection services with Cyberscout.
What neither notice states, however, is that this attack involved an extortion attempt by the BianLian group, BianLian claims to have exfiltrated 200 GB of files from VCI’s system.
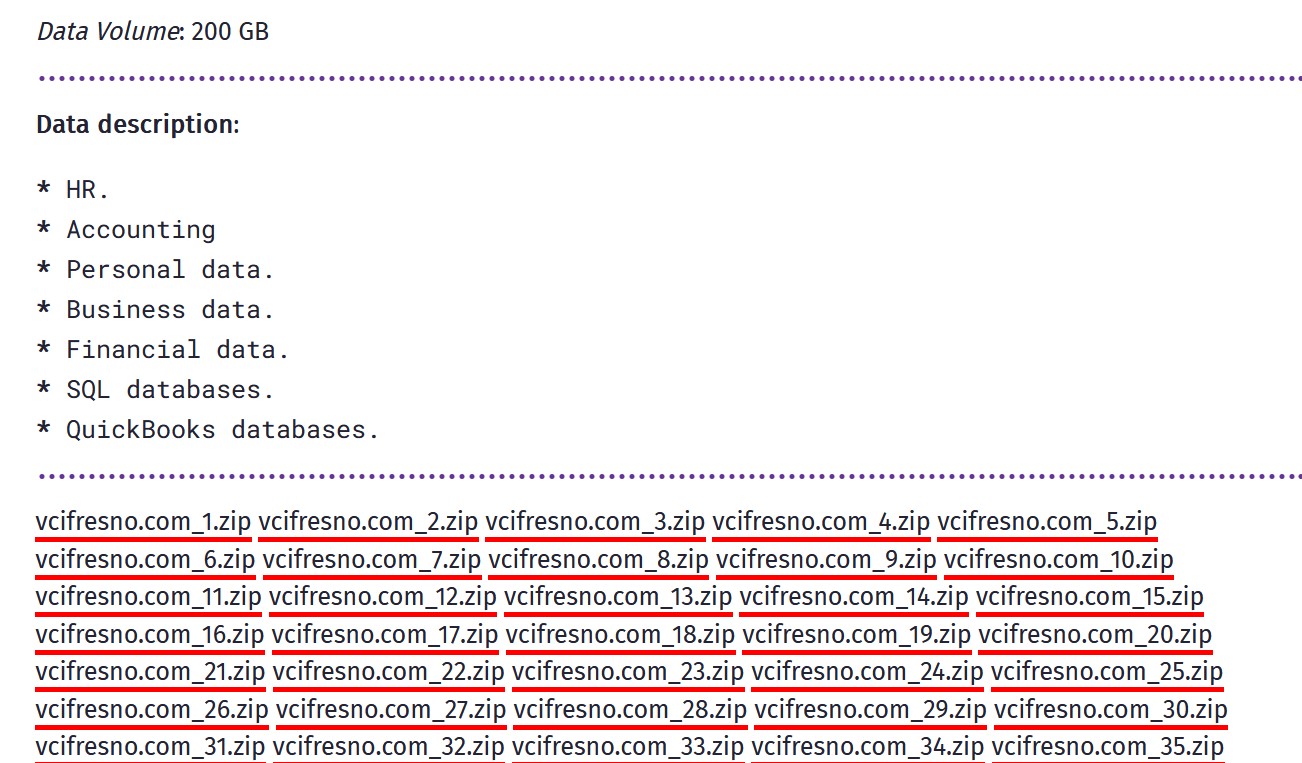
BianLian added VCI to its leak site on May 10. The VCI data appear to be dumped on the dark web site in 74 archives, but attempts to access those archives fail each time. Did BianLian really leak the data, or didn’t it?
And why didn’t VCI disclose there was a ransom demand? Why didn’t they warn those affected that the data were being leaked or would likely be leaked on the dark web by BianLian?
This incident is not yet posted to HHS’s public breach tool, so we do not know the number of patients affected. This post will be updated when more details become available.