Today’s reminder to “Tell the truth, or someone will tell it for you,” courtesy of Kevin Beaumont:
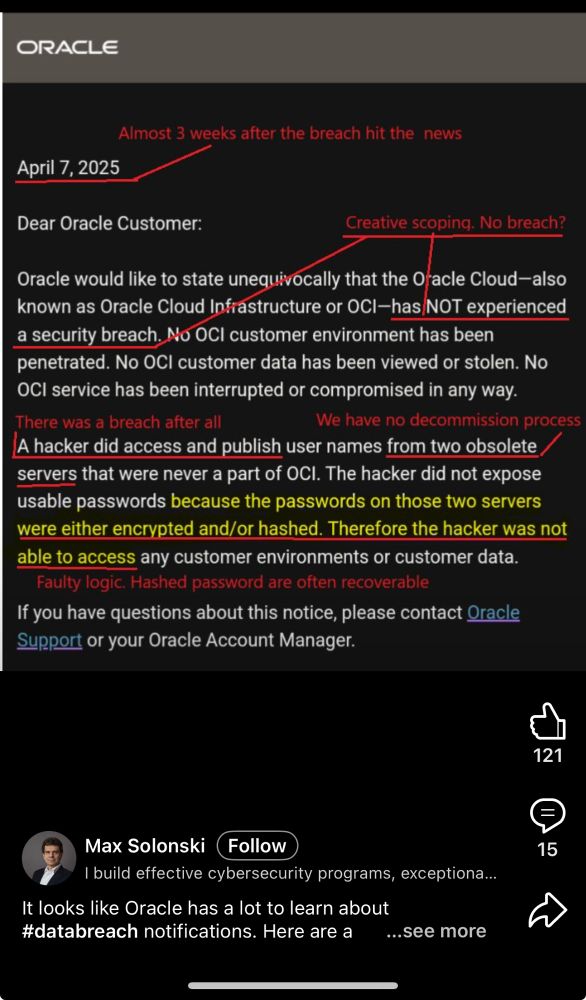
Oracle have finally issued to a written notification to customers about their cybersecurity incident. They are again wordsmithing. OCI is a different org unit in Oracle to Oracle Classic – they’re denying a different scope.
Kevin also commented:
How long was the attacker in the SaaS solution (that Oracle manage)? What did they do with the access? How long were they in for? Why were ‘legacy’ systems containing customer info left unmanaged and insecure? Etc. An exceptionally poor response for a company who manage extremely sensitive data.
Beaumont has been all over Oracle’s incident response and claims since the beginning. You can read his thread for earlier comments.
As a long-time OCI customer the BS/Reality-Distortion-Field being put up on Oracle is comically awful. The public stance is “nothing to see here!!!” while existing clients are ratting them out for ‘fessing up to the breach.
Maybe a giant hit on share price, market share or defecting customers will snap them out of their cyber-fugue?