On September 11, DataBreaches broke the story that customers of several high-end fashion brands owned by Paris-headquartered Kering had their personal information acquired by ShinyHunters as part of two Salesforce attacks. As we reported, a spokesperson for ShinyHunters claimed to have acquired more than 43 million customer records from Gucci and almost 13 million records from Balenciaga, Brioni, and Alexander McQueen combined.
Kering never responded to emailed inquiries, but ShinyHunters provided DataBreaches with samples from both attacks that appeared legitimate. They also provided chat logs from negotiations they claimed took place with someone presenting themselves as Balenciaga’s safety manager. Those negotiations appeared to go on for more than a month and a half between June 20 and mid-August. According to the logs, it appeared Kering agreed to pay a ransom of 500,000 euros, but then they went silent and never followed through.
Kering Issues a Statement
Although they did not respond to DataBreaches’ questions at the time, Kering issued a statement that they provided to other news sites, including LeMagIT and The Guardian.
Their statement, as reported by LeMagIT, does not answer all of the questions DataBreaches had, but it’s a start. Kering states:
« En juin 2025, nous avons constaté qu’un tiers non autorisé avait temporairement accédé à nos systèmes et consulté des données clients limitées provenant de certaines de nos Maisons », explique le service de presse de Kering dans une déclaration adressée à la rédaction.
Celle-ci ajoute que « nos Maisons ont immédiatement signalé cette intrusion aux autorités compétentes et ont informé les clients conformément aux réglementations locales ».
Et de préciser qu’aucune « information financière, telle que des numéros de compte bancaire ou de carte de crédit, ni aucun numéro d’identification personnelle (numéro de sécurité sociale), n’ont été compromise lors de cet incident ».
Selon le service de presse de Kering « l’intrusion a été rapidement identifiée et des mesures appropriées ont été prises pour sécuriser les systèmes concernés et éviter que de tels incidents ne se reproduisent à l’avenir ».
A machine translation roughly yields:
In June 2025, we found that an unauthorized third party had temporarily accessed our systems and accessed limited customer data from some of our Houses. Our Houses immediately reported this intrusion to the competent authorities and informed the customers in accordance with local regulations….. No financial information, such as bank account or credit card numbers, nor any personal identification number (social security number), was compromised during this incident.
According to Kering’s statement, “the intrusion was quickly identified and appropriate measures were taken to secure the affected systems and prevent such incidents from recurring in the future.”
They do not name the brands affected, they do not disclose the total number of affected individuals, and when asked what countries were affected, Kering reportedly declined to answer Reuter’s question.
An Inconsistent Statement?
It appears that neither Kering nor any of the affected brands detected the breaches on their own, and they only first found out when ShinyHunters contacted them in June. Why they did not discover the breaches by their own means is unknown to DataBreaches.
DataBreaches can confirm that there was no financial information in the samples of records that DataBreaches inspected. However, Kering’s statement to another news outlet contradicts claims made by ShinyHunters to DataBreaches.net in important respects.
As previously reported, ShinyHunters provided this site with chat logs of negotiations between ShinyHunters and someone claiming to be a representative of Balenciaga. But Kering has apparently told the BBC that it did not engage in conversations with the criminal(s), and it didn’t pay any ransom, consistent with long-standing law enforcement advice.
Their denial appears to be factually inaccurate, at least in part.
At the time of our first publication, DataBreaches reported that Balenciaga had made a small test payment in BTC to ShinyHunters. This site did not include specific proof in that article, but ShinyHunters had provided this site with evidence at the time. We are posting that proof now in light of Kering’s denial that they engaged in any conversations or paid any ransom.
The chat log provided to this site showed that Balenciaga was to make a small test payment in BTC to ShinyHunters on or about July 4. The amount mentioned in the chat log was 0,00045 BTC. The chat log also showed the BTC address as bc1qzwpshyadethrqum0yyjh7uxxzhsnjjgapdmr4c. DataBreaches had redacted that address from the published report.
On July 4, Balenciaga’s “user” told ShinyHunters that the test payment had been made:
[en attente] : 2025-07-04
[03:09:08] shinycorp: Bonjour, vous nous aviez promis un paiement hier, mais nous n’avons rien reçu. des nouvelles ?
[04:23:45] Utilisateur: Bonjour
[04:24:05] Utilisateur: nous avons eu du retard pour la création du compte
[04:24:09] Utilisateur: https://blockstream.info/tx/a4d9c24a90fdbcf652f18bafae89740094ad7a555e4e747e7e2602771e9a1d6b
[04:24:18] Utilisateur: ci joint la preuve du paiement test
[04:24:24] Utilisateur: je vous invite à vérifier
[04:52:42] shinycorp: Reçu pour la première fois
[06:17:52] shinycorp: Veuillez diffuser la transaction.
[07: 45: 06] Utilisateur: fichier: / / / C: / Utilisateurs / X / Bureau / flux de blocs.htm
[07:46:28] Utilisateur: https://blockstream.info/tx/a4d9c24a90fdbcf652f18bafae89740094ad7a555e4e747e7e2602771e9a1d6b
DataBreaches had looked up the wallet address and found confirmation of the payment. The following is a screengrab showing the payment.
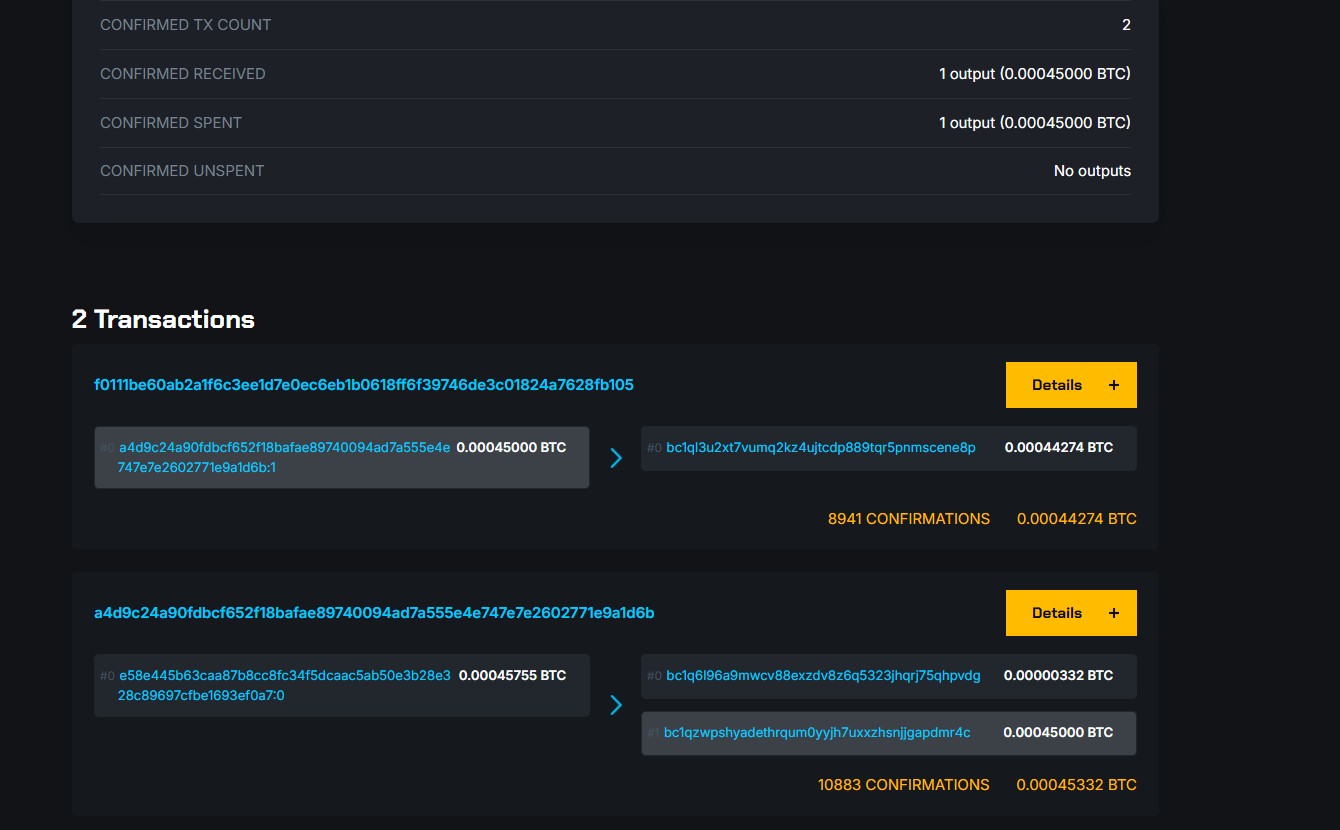
Kering’s reported claims about no conversations and no payment appear to be refuted by the chat log and corresponding BTC transaction. ShinyHunters did not claim that Kering paid their ransom demand, but they do claim that there were extensive negotiations and that a small test payment was made, and there seems to be proof of that.
Kering’s statement to other news sites also leaves a lot of other unanswered questions. They told the BBC that they had emailed all affected customers, but that raises other questions. DataBreaches emailed Kering again today to ask for additional details. Specifically, DataBreaches asked them:
- Have you notified data protection regulators in all of the countries where your customers reside?
- When did you send emails to customers to notify them?
- Have you notified store customers by postal mail if the customers did not provide email addresses? If not, how have you notified those without email addresses?
- Your statement claims that you did not have any conversations with the attackers. Has your legal department obtained IP addresses from qtox to find out the IP address of the person representing themself as Balenciaga’s negotiator? Are you claiming that ShinyHunters was lying about negotiations, or are you saying something else?
No reply has been received.
Furthermore, we still do not know how many unique customers, total, were affected by these attacks on their brands. The BBC reported that it might be less than 7.4 million based on the number of unique email addresses. But the 7.4 million unique email addresses were only for the Balenciaga, Brioni, and Alexander McQueen data. There were more than 43 million records for the Gucci data set, so there would be a significant number of unique email addresses and customers there, too, and not all customers provide an email address.
Although Kering does not seem to be embracing public transparency in its incident response, we may eventually find out more if investors demand accountability or if data protection regulators report on any investigations and findings.
We Want to Hear From You
If you received a breach notification email from Kering or one of its affected brands, please send a copy of the email to info@databreaches[.]net. We will not publish your name, but we do want to see how they explain the incident and what information they provide consumers.
Please see the update and clarification on the previous post on this subject.