Earlier today, TheDarkOverlord revealed another hack involving patient data:
Auburn Eye Care Associates of Auburn, CA. We’ve stolen many thousands of patient records from their EHR system. https://t.co/KDdIUJ59OY
— thedarkoverlord (@tdo_hackers) September 26, 2017
Auburn Eye Care Associates of Auburn, CA. We’ve stolen many thousands of patient records from their EHR system. http://www.auburneyedocs.com/
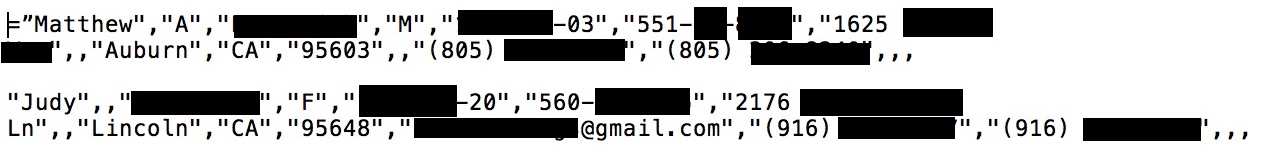
Although TheDarkOverlord (TDO) disclosed the hack today, the hack is not a particularly recent hack. TDO had first informed DataBreaches.net of this particular hack back in June, and had provided some sample patient data, a portion of which appears below as redacted by this site. The patient records included patients’ names, dates of birth, Social Security numbers, postal addresses and telephone numbers, all in plain text. For some patients, e-mail addresses were also included:
According to TDO, however, they got much more than just that database. And as they had done in other cases, TDO attempted to extort the medical practice, although the amount of BTC they demanded is unknown to this site. It is this site’s understanding that the doctors never replied to the extortion demands.
On June 30, DataBreaches.net e-mailed Auburn Eye Care Associates (AECA) to make sure that they were aware they had been hacked. AECA never responded.
More than two months later, having never seen any notice on their site or on HHS’s public breach tool, DataBreaches.net attempted to contact AECA by phone. A detailed message was left and one doctor did call back, but when DataBreaches.net returned his callback later, he did not take the call, and did not call back at all. Attempts to contact a few of the patients by e-mail also went unanswered in both June and then again today.
DataBreaches.net sent another email to AECA on September 25, asking them to respond by September 26 at 5 pm, Eastern. They didn’t. Nor did they respond to another phone message today.
So despite DataBreaches.net’s repeated efforts to alert AECA that its patients’ information had allegedly been acquired by TheDarkOverlord, this site cannot be sure whether AECA’s patients have ever been notified or if AECA has even investigated any claimed hack by TDO.
If AECA does respond, this post may be updated, but because patients appeared to be at risk and there was no indication that they have been notified of any breach, DataBreaches.net has now filed a formal complaint/request for investigation with the Office for Civil Rights. Perhaps OCR will be able to get a response from AECA where this site failed to. Hopefully, OCR will get AECA to notify patients if patients have not been notified and should have been.
