Payment card data stolen from an e-commerce platform last year has already netted criminals $1.6 million in card data sales on the dark web. And according to a new report out today, that’s just from the initial card data offering.
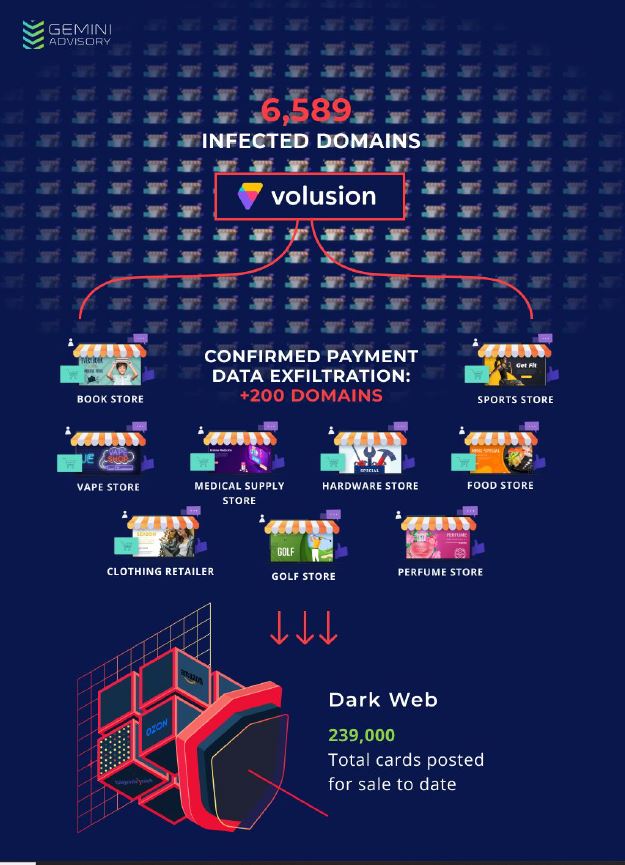
Stas Alforov and Christopher Thomas of Gemini Advisory report that a Magecart attack on Volusion that began on or about September 7, 2019 affected at least 6,589 online stores, although some reports at the time suggested that it might have impacted up to 20,000 online stores.
Gemini Advisory analysts determined that the injected script exfiltrated customer payment card data and names, including some
additional personally identifiable information such as customer phone numbers.
No compromised card data appeared on the dark web immediately after the attack, but Gemini Advisory discovered more than 239,000 compromised Card Not Present (CNP) records that were offered for sale beginning in November 2019 and continuing to the present. According to the researchers’ report:
The records came from hundreds of different merchants; several hundred have been identified as of this writing. It affected a variety of industries, from sanitation (Marine Sanitation & Supply) to sports equipment (Sunshine Golf) to monster trucks (Monster Jam Store). These stores were listed among the 6,589 merchants referenced above, and their exposure window was between September and early October 2019.
But there may be much more to come. As they also report:
The average CNP breach affecting small to mid-sized merchants compromises 3,000 records; scaling this figure to the 6,589 merchants using Volusion affected by this breach, the potential number of compromised records is up to nearly 20 million. Given this figure, the maximum profit potential would be as high as $133.89 million USD.
That estimate is based on 6,589 merchants. What if the reports suggesting that even more online stores were compromised were correct? Then the numbers may be significantly higher. The figure below, from Gemini Advisory’s report, indicates that more than 200 domains and a range of businesses. were represented in the stolen payment card data.