The Yomiuri Shimbun reports:
Capcom Co., an Osaka-based major game software maker, announced Monday that up to 350,000 pieces of information, including those of its customers, might have been compromised by cyber-attacks.
The company said the potentially stolen data includes its customers’ personal details, such as names, telephone numbers and email addresses.
The company also revealed that it had been threatened by an attacker using ransomware, a computer virus used to demand money in exchange for stolen data that is essentially held hostage.
Read more on Japan News.
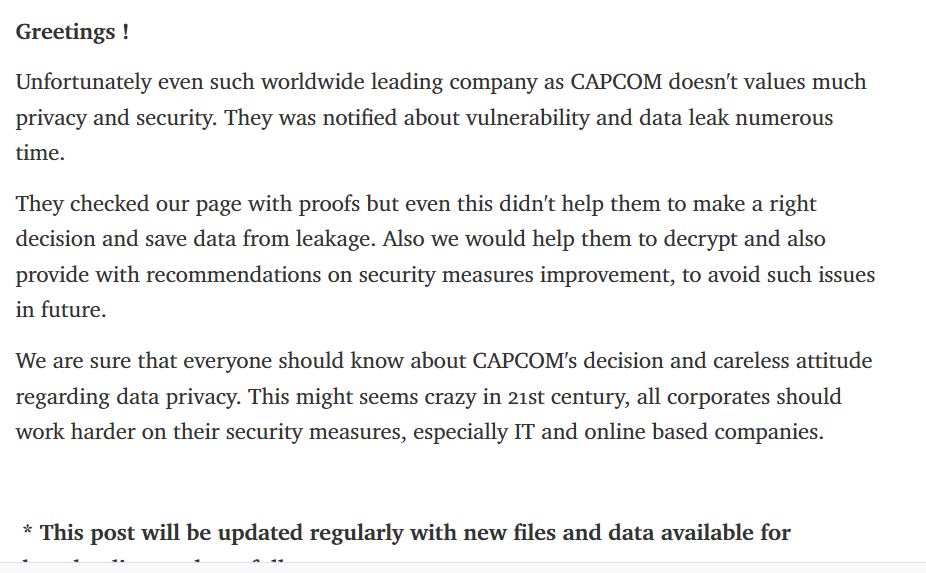
As these groups tend to do, Ragnar_Locker threat actors monitored Capcom for their response, and then dumped more data with a statement on their dedicated leak site. As of today, it appears that the attackers have dumped approximately 60 GB of data.