Earlier today, video game developer CD Projekt Red announced on Twitter that it has been hacked and a ransom demand received.
“We will not give in to the demands nor negotiate with the actor, being aware that this may eventually lead to the release of the compromised data,” they write, adding that while they are still investigating the attack, “the compromised systems did not contain any personal data of our players or users of our services.”
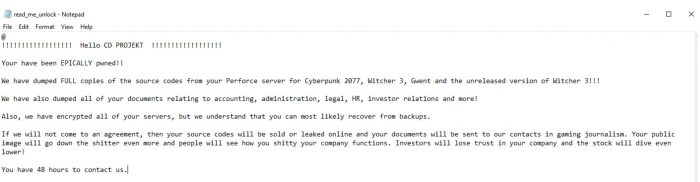
The ransom note claims that the threat actor(s) have obtained the source code for the firm’s games, as well as all HR, accounting, and other documents. Interestingly, the note seems to acknowledge that the firm will likely be able to restore from backup.