David Simmons reports:
A ransomware attack called LockBit 2.0 has hit multiple organisations across various industry sectors according to the Australian Cyber Security Centre (ACSC), with the government body publishing a ‘medium’ alert for the cybercrime.
[…]
Operators of the platform have appeared on Russian-language cybercrime forums since January 2020 according to ACSC, but the ‘2.0’ version of LockBit was released in June this year bundled with a built-in information stealing function called ‘StealBit’.
“The ACSC is aware of numerous incidents involving LockBit and its successor ‘LockBit 2.0’ in Australia since 2020.
Read more on Business News Australia.
Lockbit2.0’s leak site on the dark web certainly shows a lot of recent activity. In the partial screencap below. redacted by DataBreaches.net. victims listed in red are those who the threat actors are trying to pressure by publicizing the breach.
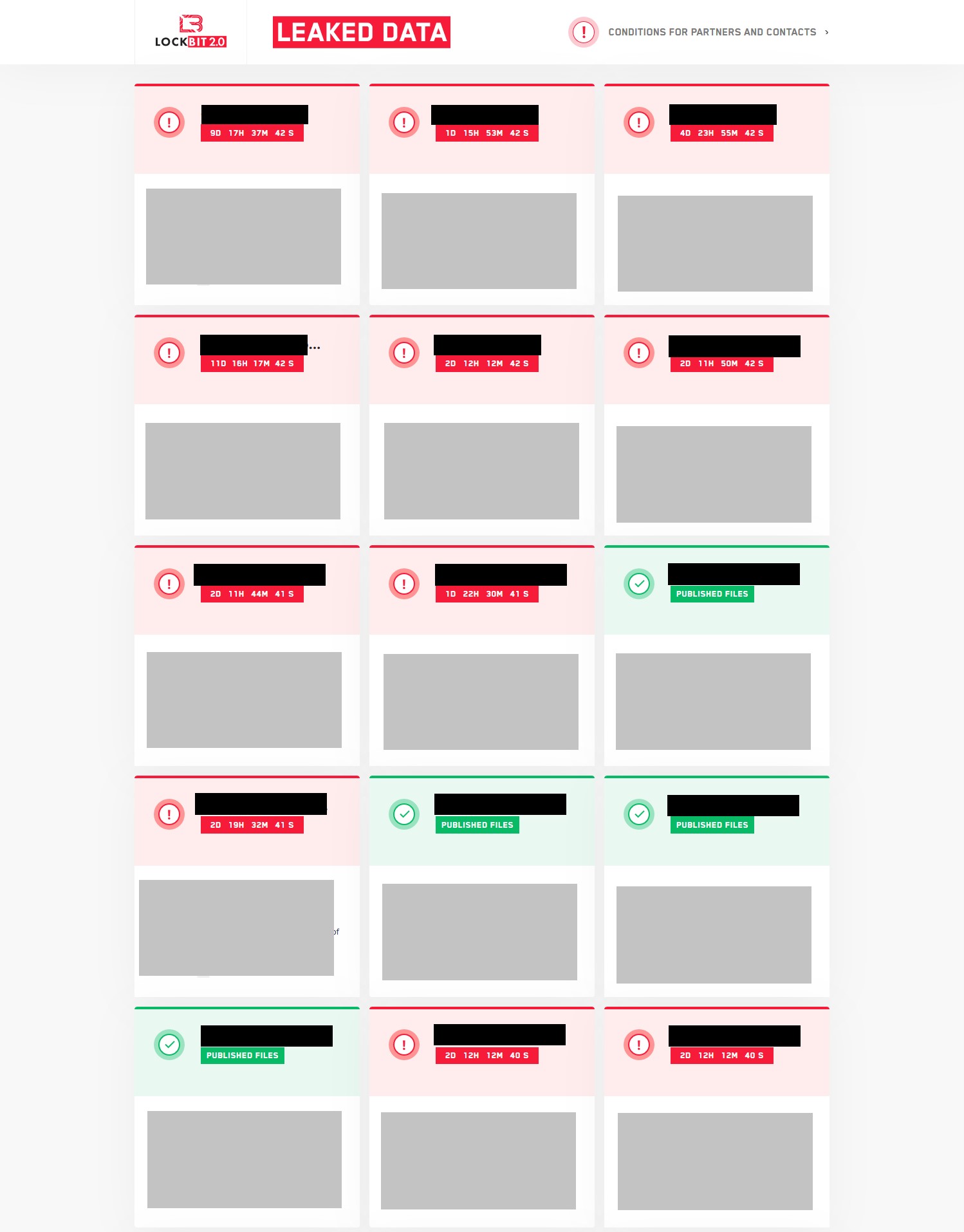
Those listed in green are those victims who didn’t pay and whose stolen data is being dumped for people to freely download. The screencap is just the top portion of a verrrrry long web page of listings.