On May 15, Chum1ng0 reported that German furniture retailer Möbelstadt Sommerlad had been hit by DarkSide threat actors. By then DarkSide’s leak site was down and it had not been possible to confirm whether DarkSide had ever listed the retailer as a victim or dumped any proof of claim, but given the time frame of the attack and the takedown of DarkSide’s site, it seemed unlikely that they had ever been listed. It was the owner of the furniture store who named DarkSide as the threat actors, and who stated that the firm would not be paying any ransom.
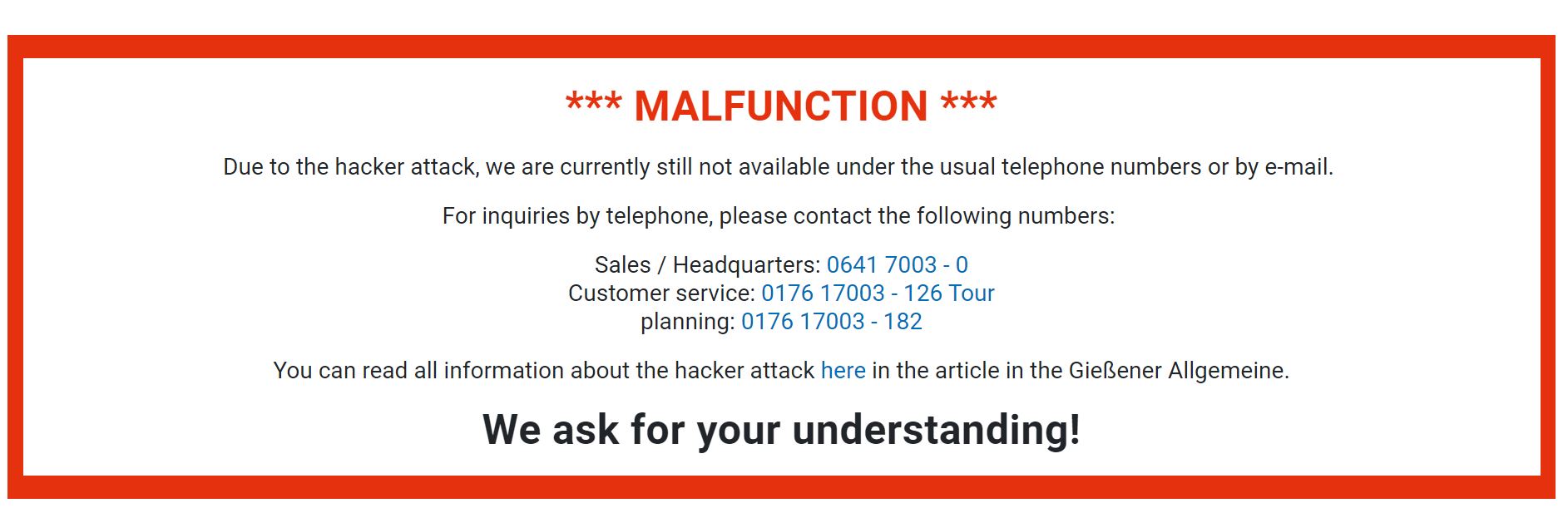
As of today, the notice saying that the store is still not functioning remains on their web site (the English version):
But also of note, today Chum1ng0 noticed that REvil (Sodinokibi) threat actors listed this attack as their work, and claim to have more than 175 GB of data:
We downloaded a lot of interesting information from your network. All data are fresh and will be stored on our CDN servers for the next 6 month if you do not pay.
If you need data leak proofs, we are ready to provide them.

Consistent with their usual practice, they provided some screencaps of file trees.
The fact that they listed the firm on their leak site suggests that Möbelstadt Sommerlad’s owner has not changed their mind and is continuing to refuse to pay any ransom, but without email and with their Facebook page not available, it’s difficult to confirm this with them.

What the listing by REvil does confirm, however, is some frequent speculation that DarkSide and REvil had a collaborative or cooperative relationship somehow. Did one of DarkSide’s affiliates now take their data to REvil to help them with the extortion attempt? Perhaps.
In collaboration with Chum1ng0. Post-publication, I learned that this was first reported on Twitter by @z0man, so credit to him.