UPDATE: Sometime earlier today, after my communication with RansomHub, they removed the April 15 update described in the post from their listing. It has now been replaced with a note:
Change HealthCare – OPTUM Group – United HealthCare Group – FOR SALE
The data in now for sale. Anyone interested in the purchase should contact RansomHub.
When Change Healthcare was the victim of a ransomware attack in February, it was a “double extortion” attack. Systems were encrypted, and data was exfiltrated. According to an affiliate who claimed to be responsible for the data exfiltration, AlphV locked the systems and conducted the negotiations with Change Healthcare on behalf of themself and the affiliate who had done the exfiltration. But then AlphV allegedly made a deal with the victim, took the money, and ran after allegedly only giving Change Healthcare a decryptor key. The exit scam left Change Healthcare without their data returned or destroyed, and left the affiliate without any pay for the 4 TB of data they claimed to possess.
Change Healthcare has never confirmed nor denied paying $22 million for a decryptor key, but there was some evidence of a payment of that size at that time.
More than a month later, a listing appears
This week, a listing appeared on a dark web site by RansomHub. The initial listing made it sound like they had the 4 TB of data from Change Healthcare:
As an introduction we will give everyone a fast update on what happened previously and on the current situation.
ALPHV stole the ransom payment (22 Million USD) that Change Healthcare and United Health payed in order to restore their systems and prevent the data leak.
HOWEVER we have the data and not ALPHV.
The data consists of over 4 TB of highly selective data. The data relates to all Change Health clients that have sensitive data being processed by the company.
There was more to the listing, but they did not provide any proof of claims at the time and did not provide any proof to DataBreaches when this site reached out to them on April 8 to request some proof of claims.
What they did do is give some data to WIRED, who reported on the listing and said the data look credible to them. But WIRED’s story seems to have confused some people into thinking that there was a new — a second — attack on Change Healthcare. Change Healthcare claims they have no indication of any second attack, and there was nothing in RansomHub’s initial listing to suggest anything other than they had the 4 TB of data from the original attack on Change Healthcare. But even that raises questions. Had the affiliate known as “notchy” gone over to RansomHub with the data for them to list on their site? If not, how did RansomHub get the data?
Shooting themselves in the foot?
Attempting to increase pressure on Change Healthcare to pay them, RansomHub posted an update on April 15. In it, they wrote, in part:
The more we go through the data the more we are shocked of the amount of financial, medical, and personal information we find and it will be more devastating than the first attack itself.
They also leaked a number of files with protected health information (PHI) and internal documents. When this breach is investigated by HHS, one of the questions DataBreaches hopes they ask is why there was so much old PHI stored without encryption or offline. One of the screencaps related to Medicare claims for dates of service from 2011-2013. Patients’ names do not appear in the screencap, but perhaps other files in the leak would enable identification of patients and details on claims such as diagnoses or treatment codes.
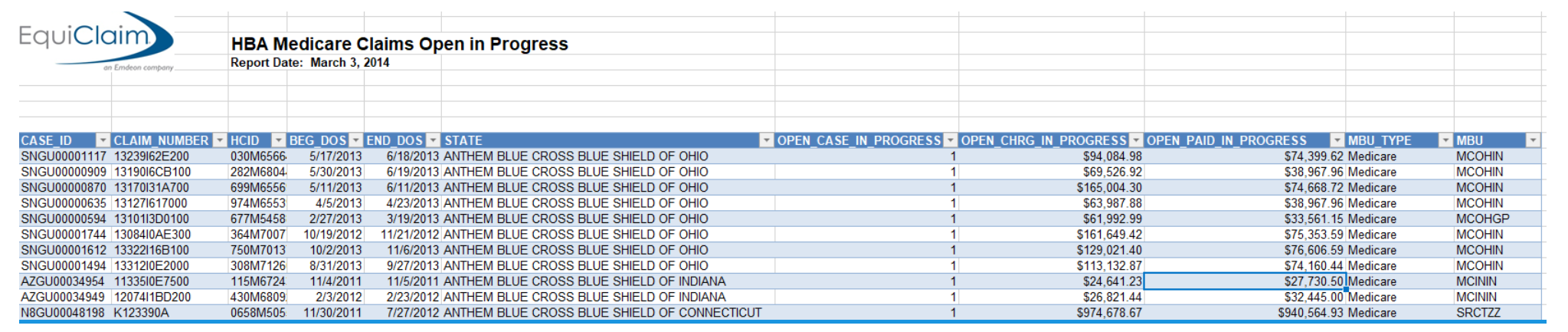
Other screencaps in the updated listing show more recent transactions and patient names and other details.
But what did RansomHub mean by comparing this to “the first attack itself?” Are they saying this was from a second and more recent attack? DataBreaches suspected that this was just a problem with English and that they meant that any data leak would be more devastating than the locking. Of course, even that makes no sense when one considers the impact of the encryption of the systems and its widespread and significant impact on providers, pharmacies, and patients. But what do we make of the second listing?
DataBreaches reached out to RansomHub again last night to seek clarification, asking:
Are you saying that there has been a SECOND attack on Change Healthcare that also managed to get 4 TB of data? Or are these data the original data that “notchy” claimed to have exfiltrated originally? And are you notchy? If not, how did you get the data?
RansomHub responded this morning that there will be major updates on the blog today. Given that researchers and analysts have been expressing confusion and suspicion about the authenticity of their claims and data, it would have been wiser for them just to answer the questions directly.
If RansomHub hasn’t been forthright in answering some straightforward questions seeking clarification, why would Change Healthcare (or any victim) believe that RansomHub can be trusted to delete any data if they were paid? Given how many times threat actors swear they will delete data but never do, paying extortion to delete data is like just giving criminals a gift of free money. In this case, the threat actors are a fairly unknown group with no reputation to cite. Has Change Healthcare even responded to them at all?
Congress will, of course, hold hearings
The House Energy and Commerce Committee is holding a hearing today, “Examining Health Sector Cybersecurity in the Wake of the Change Healthcare Attack.” The hearing will be livestreamed at https://energycommerce.house.gov/ beginning at 10:00 am Eastern. The witness list has not yet been announced.
The Senate Finance Committee will also be scheduling a hearing soon.