The bar has been lowered. Which bar, you wonder? The bar for how low entities will sink rather than just saying they experienced a ransomware attack.
Minneapolis Public Schools will open for in-person instruction as usual Monday, after a week of disruptions from “technical difficulties” and snow.
In an email to families and students, Minneapolis Public Schools described the technical issues as an “encryption event.”
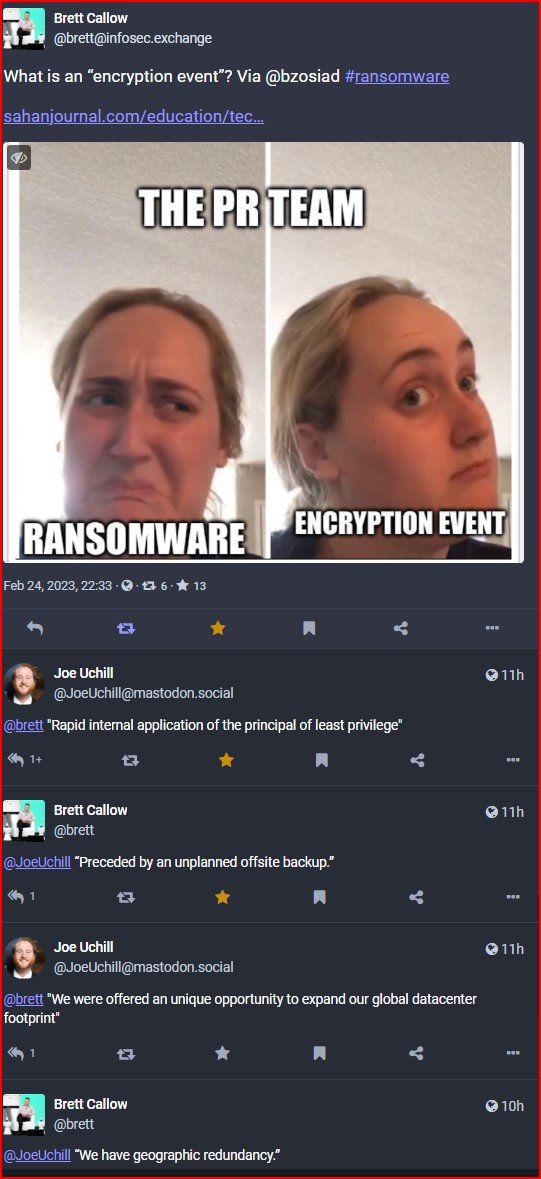
What is an “encryption event”?
“I don’t have any specifics past that,” a district spokesperson told Sahan Journal.
That’s not surprising since, to DataBreaches’ knowledge, that is the first time “encryption event” was used to describe an incident instead of just saying “malware” or “ransomware.”
The district’s evasive language led to some snark and hilarity on infosec.exchange, where Brett Callow and Joe Uchill suggested alternative evasive language.
Of course, a ransomware attack or malware attack is not a laughing matter but neither is an attempt to spin a data security incident. It is time for districts to cut the b.s. and just tell parents and employees the unvarnished truth.