Over the past few months, I have regularly checked Maze Team’s website to see if any of the entities they are listing are in the healthcare space. As I reported in the past, Maze Team did hit a number of healthcare-related entities, not all of which have been named on their website. But there were two entities who had been named on their site at one point and then… no longer appeared.
One of those victims is Crossroads Technologies, a business associate to HIPAA-covered entities. As I reported previously, Crossroads kept ignoring all of this site’s inquiries, even though I know they received those inquiries. Eventually, and as I also reported, 17 Personal Touch Home Care units reported the Crossroads breach to HHS and state regulators. The Personal Touch reports accounted for almost 157,000 affected patients reported to HHS.
But Maze Team never dumped all that data, and in fact, their entry for Crossroads disappeared at some point. I asked them why, and their answer was a bit of a surprise. They wrote:
Long story short, they haven’t completed the last part of our deal, but out of ethical reasons we have decided to leave them alone, we actually provided some free recovery to their clients hospices etc.
So Crossroads allegedly didn’t pay everything that had been demanded, attackers did not dump more data, removed their listing, and even helped some of the hospices? That would be pretty stunning, and it would be nice to get some confirmation of their claim. If any of the Personal Touch Home Care units are willing to confirm their claim, we’d love to hear from you.
But Crossroads wasn’t the only medically-related victim entity that disappeared from Maze Team’s website. DataBreaches.net had also noticed that Stockdale Radiology no longer appeared on the site. Maze Team had first informed DataBreaches.net about the Bakersfield entity on January 18 via email, and I reported on it on January 28 after they were added to the hackers’ website.
So what happened with them? In response to my inquiry as to whether Stockdale Radiology was removed from the site because they paid up or for some other reason, Maze Team replied (typo corrected in the following):
Indeed we have reached an agreement with them. Their data was removed completely.
Stockdale has not posted any substitute notice on their website, and there has been no report to the California Attorney General’s Office. Nor is there any notice from them on HHS’s public breach tool. DataBreaches.net’s attempts to reach them were not successful.
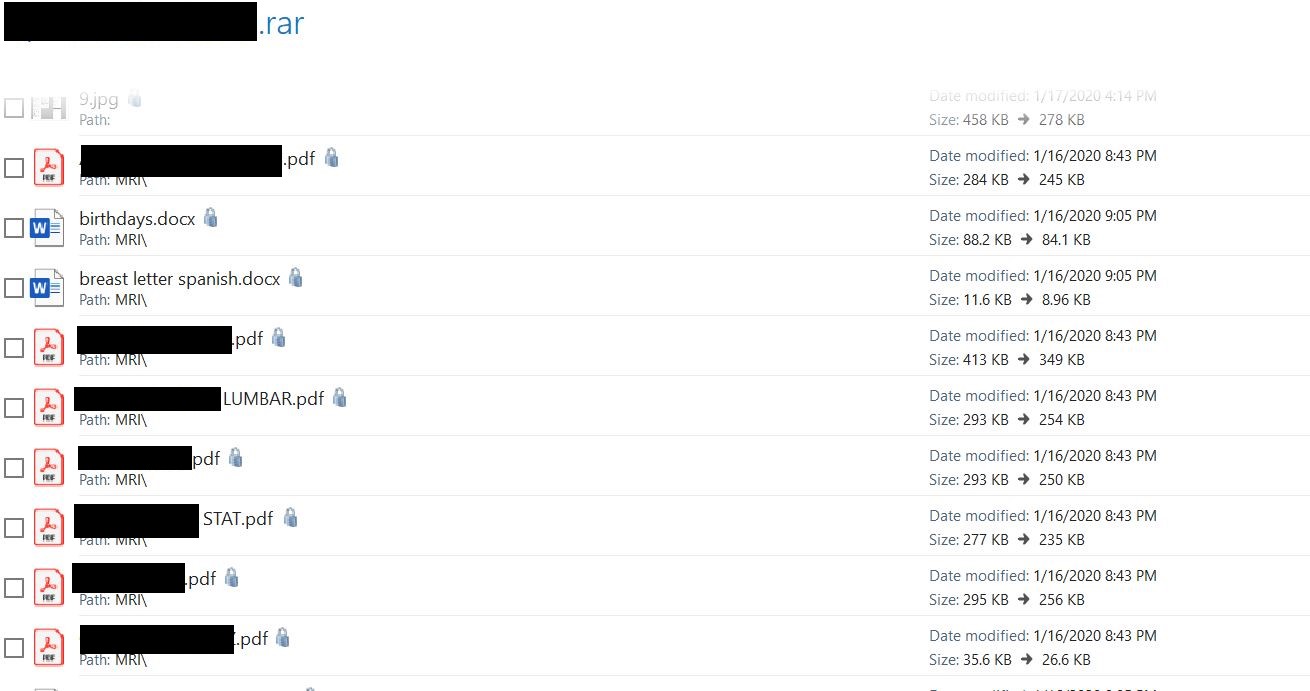
If Stockdale Radiology was attacked on or before January 17, as appears to be the case from data that was used as proof of hack, then Stockdale Radiology should be notifying patients and HHS no later than March 17 (assuming that they learned of it promptly). We’ll be watching to see if they do disclose, because even if they paid the ransom, patients’ protected health information still left their control. Do they even know how many unauthorized individuals have their patient data or what patient data was shared? Some of the files I viewed were multi-page documents with patients’ detailed histories of back issues or concerns that required testing — in at least one case, “STAT!”

The Stockdale Radiology claims will be updated as more information becomes available.
Update of March 30: HHS added a report file by Stockdale Radiology on March 27. It indicates that 10,700 patients were affected by the ransomware attack.