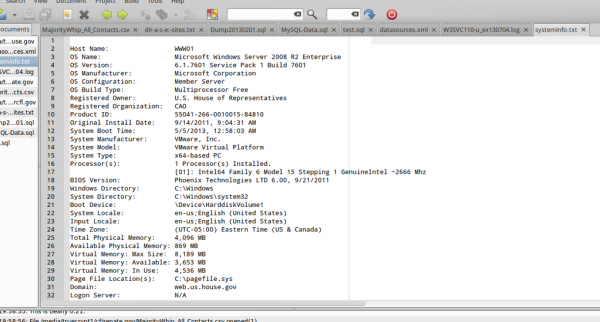
While many of us were watching the House Judiciary Committee oversight hearing on FISA, @OpLastResort tweeted:
While the House Judiciary Committee held #FISAOversight hearings today, we’ve been doing some oversight of the House pic.twitter.com/obWimEBjTf
— OpLastResort (@OpLastResort) July 17, 2013
Today, Richard Cowan reports:
Congressional aides in the Senate and House of Representatives said on Thursday that they were notified of a potential security risk involving email and other accounts.
“There have been reports online of Senate and House email accounts being exposed and hacked,” said an email warning sent to all Senate staff.
The memo added, “no account or data has been accessed or stolen.” But the memo warned that the posting of congressional email addresses often leads to “future targets of spear phishing,” a type of electronic fraud targeting specific organizations.
Congressional employees were warned to forward suspicious emails to security officials so they could be screened.
A long list of congressional email accounts, some belonging to former employees, was posted on at least one website. Many of the email addresses also listed what appeared to be passwords.
A tweet by OpLastResort warned: “Dear #Congress: We are paying very, very close attention to how you handle #NSA #FISA & #PRISM Don’t.. Fuck.. Up….”
Read more on WKZO
In the paste of e-mail addresses and alleged passwords, @OpLastResort writes:
“NOTE: FOR THE PURPOSES OF BEING FAR TOO GENEROUS WITH YOU GUYS, WE HAVE REMOVED SOME OF THE PASSWORDS AND SHUFFLED THE ORDER OF THE REMAINING ONES. THESE ARE ALL CURRENT, VALID CREDENTIALS BUT THEY ARE NOT IN THE ORIGINAL PAIRINGS. WE RESERVE THE RIGHT TO SPONTANEOUSLY DECIDE THIS RESTRAINT WAS UNJUSTIFIED.”
The Hill, however, reports that the data may not have been stolen from House’s email system:
An email that was sent to congressional offices, obtained by The Hill, said House Security believes the leaked staffer emails and passwords were poached from another online service rather than the House network’s email system.
A separate email sent to House offices said the breach was traced to the iConstituent newsletter product, which is typically used by press staffers to communicate with constituents.
The email urged staffers to change their password for the iConstitutent service and said their email accounts on the House network were not affected by the breach.
Read more on The Hill.
Update: @OpLastResort just confirmed to DataBreaches.net that the iConstituent service was the source of the data they dumped.