NullCrew has responded to Bell’s claim that it was a third-party supplier who got hacked by providing DataBreaches.net with more details about the hack and their conversations with Bell alerting them to the breach.
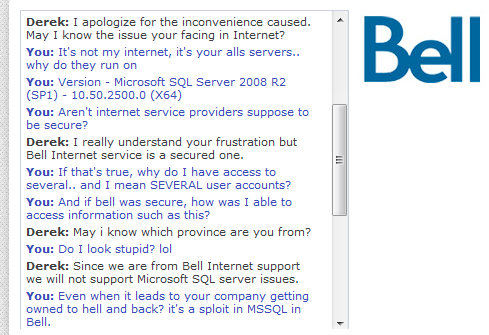
In an interview today, NullCrew revealed that they had access to Bell’s server for months, and had disclosed that to them in a chat with Bell Support weeks ago. A screenshot of the chat between NullCrew and Bell Support employee “Derek” shows that NullCrew was informing Bell that they were in possession of users’ information:
NullCrew states they actually gave them the vulnerable url and details, but got nowhere with them.
I informed them they didn’t have much time, and the world would soon see their failure…. Their response was exactly what you see in their article, bullshit. “Bell Internet is a secure service.” They did not even say they would look into it, they did not try and assess the exploit.. it was up, for two weeks. And only taken down after we released our data.
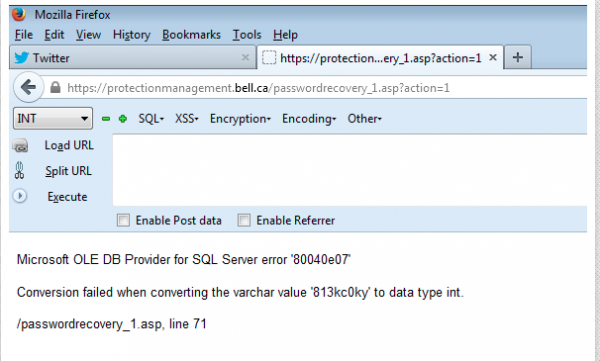
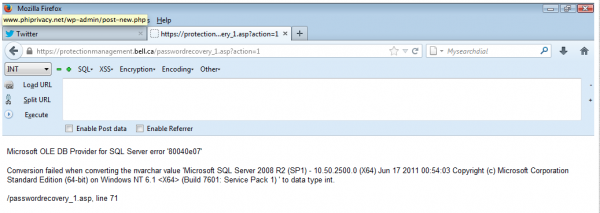
NullCrew informs DataBreaches.net that the attack was by POST SQL injection. The vulnerable url was Bell’s protection management login page: https://protectionmanagement.bell.ca/passwordrecovery_1.asp. Bell’s protectionmanagement subdomain is currently unavailable.
As proof, NullCrew provided DataBreaches.net with screenshots taken at the time (all screenshots in this article are copies of the screenshots provided to this site):
So what is Bell talking about in their statement where they claim they were not hacked but a third party supplier’s system was? The screenshots support NullCrew’s claim that it was Bell’s server that was successfully attacked. Bell has not yet responded to an email inquiry sent by DataBreaches.net asking if the third party supplier they mention would come forward and confirm their statement or if Bell would name the third party.
Right now, then, it appears that customers may have good reason to question Bell’s version of the breach. “Who are you going to believe, companies, corporations, big brother? Or the people who fight against this system?” NullCrew asks. [See update below post for Bell’s response – Dissent]
And other big corporations may want to take note that the Bell attack may just be the beginning. NullCrew wants us all to know:
NullCrew is far from done, we want to make it evident that just because we lurked in the shadows; it does not mean we left. That we are here to stay. Simply put? Stay tuned. #FuckTheSystem is just beginning.
Update 1: Bell Canada was sent a link to this report and asked if they still stand by their statement of this morning. They do:
Yes, we stand by the facts in our release. The posting results from illegal hacking of an Ottawa-based third-party supplier’s information technology system.
Update 2: Adam Caudhill points out that it’s not uncommon to find a subdomain of a large company pointing to a third party. “So it’s quite possible they are telling the truth. They should still take more responsibility for their data though,” Adam tweeted.
A lookup of protectionmanagement.bell.ca resolves to IP 206.191.10.10, which is registered to Magma Communications in Ottawa, a subsidiary of Primus Communications. Interesting.
So Happy there is a group of people out there that can prove that major companies that claim they are secure and perfect are useless/defenceless in reality. Their arrogance is their own downfall. FUCK THE SYSTEM!
That’s the stupidest disclosure imaginable… Bell knew about it because NullCrew blustered about their l33t spl01ts to the web chat support team?
Most likely some poor schmuck in Bangalore, didn’t really understand what was being said so kept on parroting back the most appropriate scripted answer.
As Adam Caudill tweeted to me yesterday, Bell may be lacking an appropriate escalation policy for Support that tells them what to do with such reports. I don’t know if that’s the case, but I wouldn’t be surprised in light of all the trouble I and others have had over the years trying to alert entities to security breaches.
No doubt about Magma.they’re the GoDaddy of Ontario
http://toolshack.com/206.191.10.10
http://myip.ms/info/whois/206.191.10.0
Let’s suppose you go to a fast food chain and the food is really bad and stinky and the facility manager tells you it’s ok. Are you going to look up the franchise owner or call headquarters? Well…
No.
Lets suppose I go to a fast food chain, and the deep fryer and/or grill are dirty, unsanitary and makes the food taste bad. The facility manager indicates that it’s OK to their standards.
Are you going to call the franchise owner to speak with them (again)?
Are you going to call the franchise HQ to speak with someone there?
or..
Are you going to call the company that makes the deep fryer and/or grill?
The most logical response (in my opinion) would be to consult the franchise HQ, as they set the standards on what equipment is used to prepare their food. The facility manager would maintain that equipment as per their standards, and the manufacturer of the equipment has recommendations on how to maintain it.
Contacting a facility manager keeps the issue isolated, and it can often lose momentum here.
Contacting the HQ will cause an internal investigation as to the quality and/or sanity of the equipment, in which the facility manager would likely have no say, and would be required to abide by their requests.
——–
TL;DR
Bell allows this 3rd party hosted server to be used in their network infrastructure, including storing their customers sensitive information here – they are responsible for this.
Exactly.
thats the scary part….
Magma has colo services and their own clients, that is probably why the IP points to them. Must be one of their clients that is the mentioned 3rd party.
Looked like 10Count Consulting to me.