As if it couldn’t get any worse for Avid Life Media, a second data dump has been released on the dark web. This one appears to contain all of CEO Noel Biderman’s emails and the source code for their web sites.
As Trusted Sec notes on their blog:
if this turns out to be legitimate which it in all aspects appears to be – having full source code to these websites means that other hacker groups now have the ability to find new flaws in Avid Life’s websites, and further compromise them more.
Today’s data dump appears to be a response to a statement made by ALM’s former CTO Raja Bhatia to Brian Krebs after the first dump denying that the 9.7 GB data dump was real. ALM subsequently walked that claim back, simply claiming that AM never stored full credit card numbers.
In today’s message, the hackers, who PGP-signed their message, write,
“Hey Noel, you can admit it’s real now.”
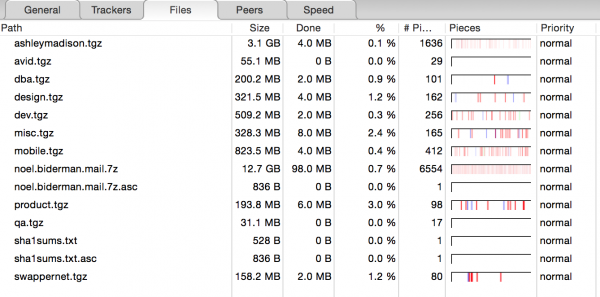
This screen cap of the torrent contents shows suggests that this dump is solely corporate and proprietary information. Note the 12.7 GB file labeled noel.biderman.mail:
 At the time the hack was first disclosed, AshleyMadison stated that they believed that it was an insider who was responsible for the hack. Since that time, they have not really expanded on that claim or walked it back, saying only that they are working with law enforcement in both Canada and the U.S.
At the time the hack was first disclosed, AshleyMadison stated that they believed that it was an insider who was responsible for the hack. Since that time, they have not really expanded on that claim or walked it back, saying only that they are working with law enforcement in both Canada and the U.S.