The free market system might appear to be alive and well on the dark web. As sites like LeakedSource add newly leaked databases from hacks in 2012-2015, we are also likely to find the databases up for sale on sites like dark web marketplaces. For current examples, see the listings for the Dropbox database and BitcoinTalk forum database:

Of course, a listing by itself is no guarantee of authenticity, and most sellers offer a sample for verification purposes.
Although it might appear that there’s competition in selling, don’t rule out the possibility or likelihood that two vendors offering the same database for sale may actually be the same seller listing under different names to encourage purchase of the databases at the lower prices as if they’re a better deal. Some of these sellers are continually appearing under new aliases or contract with others to re-sell for them for a percentage.
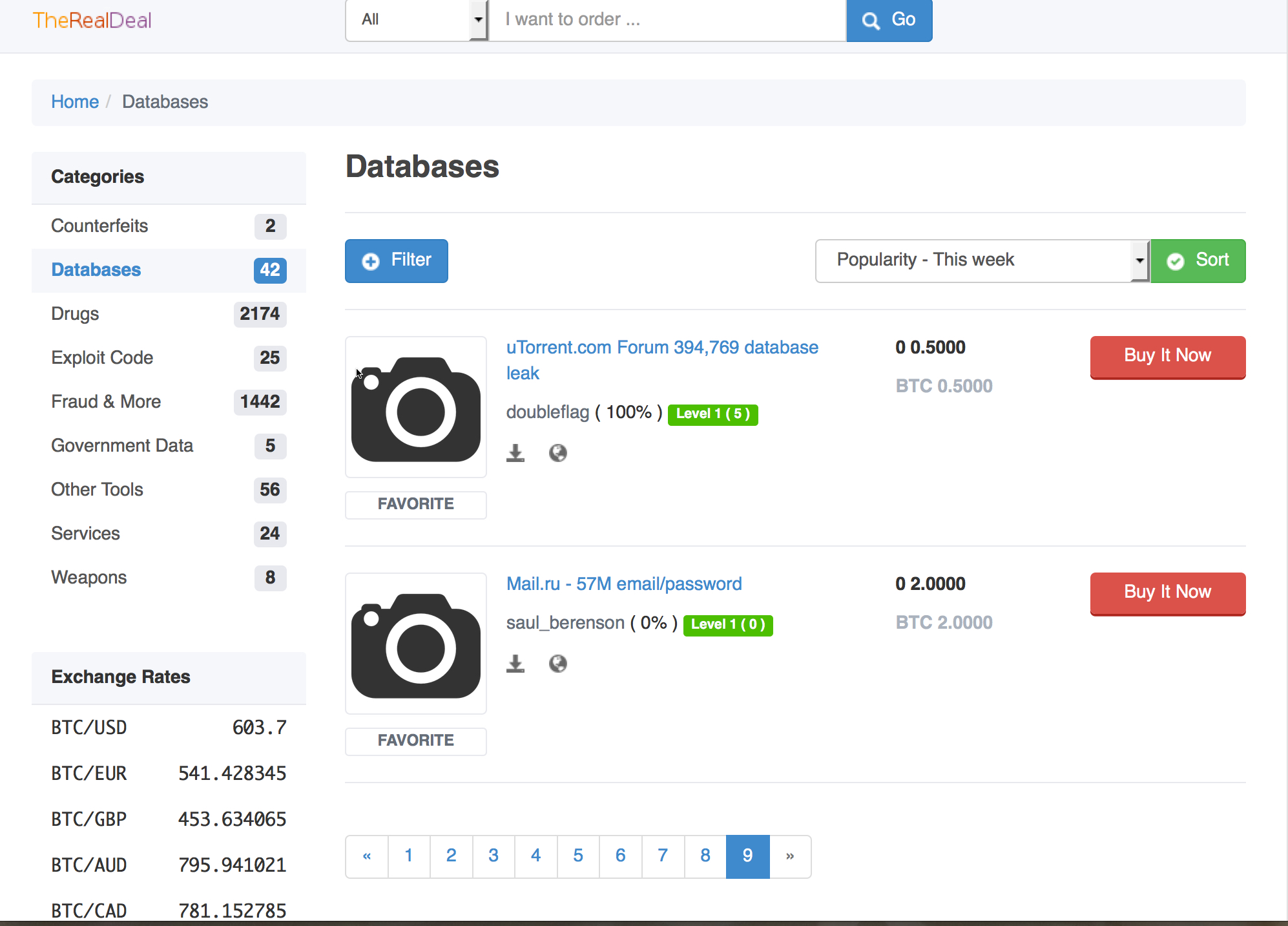
The uTorrent and Mail.ru databases, or databases purporting to contain the data, have also been listed for sale this week:
With so much data flooding the market, the price of personal information like email addresses and passwords drops. Even the price of databases containing more stable information like SSN appears to have dropped. And scary headlines notwithstanding, from what I’ve seen on some marketplaces, there doesn’t seem to be much interest or many buyers for actual medical information or patient records, apart from their potential value for identity theft or fraud (unless, of course, we’re talking about a celebrity’s or politician’s records). Old claims about medical records going for $50 per record do not appear to be accurate at all in today’s current market. Even name, SSN, and date of birth are often not enough for identity theft, and criminals may need other sources of information so that they can answer security questions requiring knowledge-based answers (KBAs) such as first school, first pet’s name, etc.
But assuming you are not interested in buying these databases, but just want to protect yourself, as you still re-using passwords you used in 2012 on some sites? Have you learned to use throwaway or tagged email addresses with unique passwords for each site you register for? If not, why not?