Another day, another leak.
It appears a security researcher who searches for leaks on public FTP servers has uncovered another leak involving personal information. This time, it’s the personal information of 11,771 individuals who applied to the State of Nevada Medical Marijuana Program to become an agent for a medical marijuana establishment (MME).
The researcher announced his finding on Twitter and sent a message to this site, seemingly thinking that it was medical information on patients, which it is not. Under Nevada law, “a Medical marijuana establishment agent” means an “owner, officer, board member, employee or volunteer of a medical marijuana establishment, an independent contractor who provides labor relating to the cultivation or processing of marijuana or the production of usable marijuana, edible marijuana products or marijuana-infused products for a medical marijuana establishment or an employee of such an independent contractor. “(NRS 453A.117)
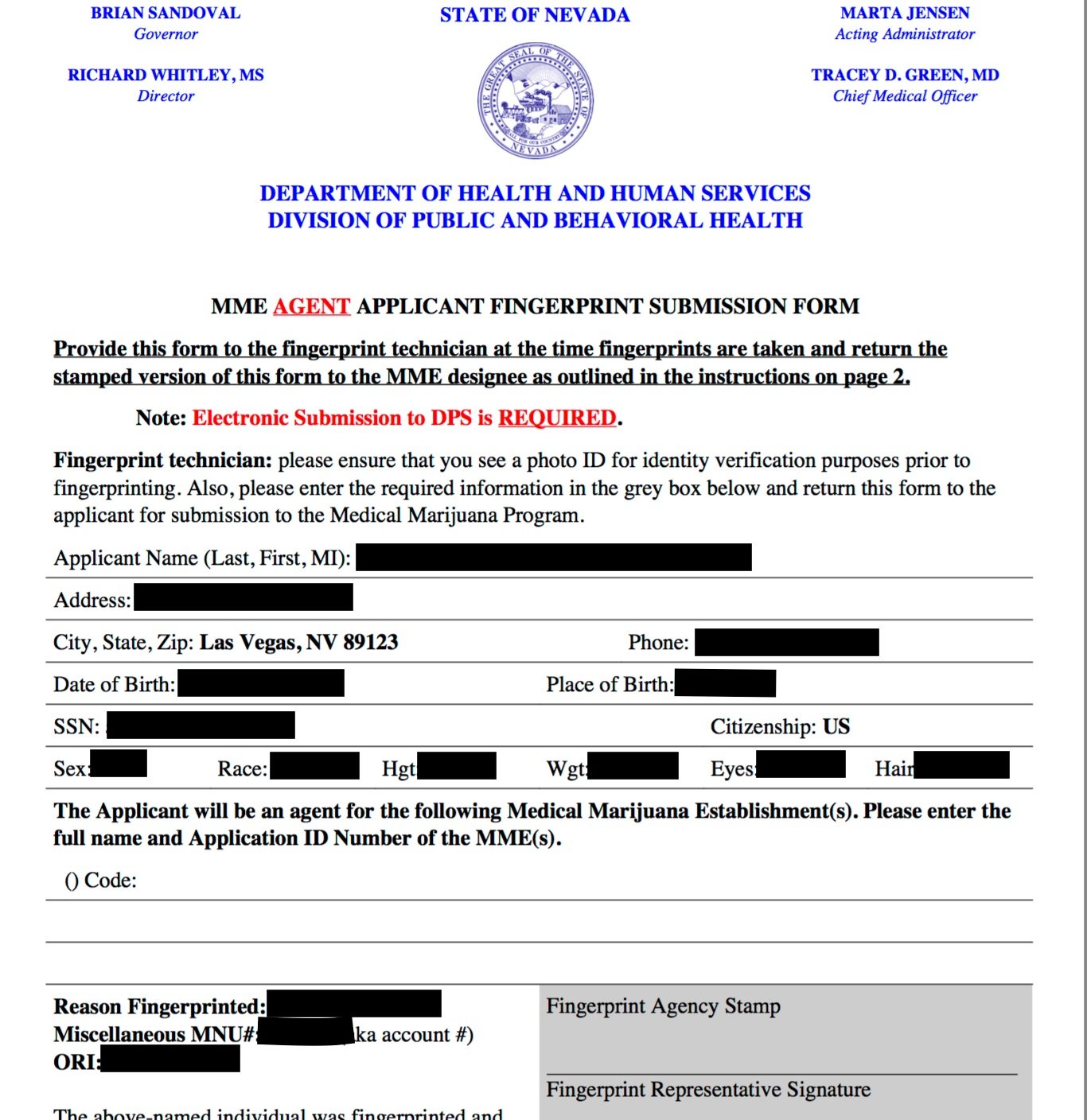
Although not patient data, the wealth of personal information on the applicants makes this a concerning leak. The application forms include the applicants’ name, position, physical and mailing addresses, date of birth, Social Security number, telephone number, citizenship, hair and eye color, height and weight, and their driver’s license numbers. Applicants also also submit their photos and signatures, which do not appear to be in the exposed files. Applications for fingerprinting or notation that fingerprints are on file are also included, as the following screenshot, redacted by DataBreaches.net, shows:
Simple url manipulation would allow people to obtain applications, allowing for potential scraping and acquisition of all the data.
DataBreaches.net verified that the data in an exposed application was valid via a voter records check on the named individual. Andrew Couts of The Daily Dot also reported that he had verified the accuracy of the data.
The state’s Medical Marijuana Program is under the Department of Health and Human Services Division of Public and Behavioral Health.
DataBreaches.net contacted the state and in addition to leaving voicemails with their IT security and DHHS, spoke with someone on their 24-hour security helpdesk who indicated they would escalate the message about the exposed files. Approximately one hour later, the files were no longer accessible.
This report will be updated as more information becomes available.
Update: Zack Whittaker got confirmation from a spokesperson that applicants will be notified in the next few days.