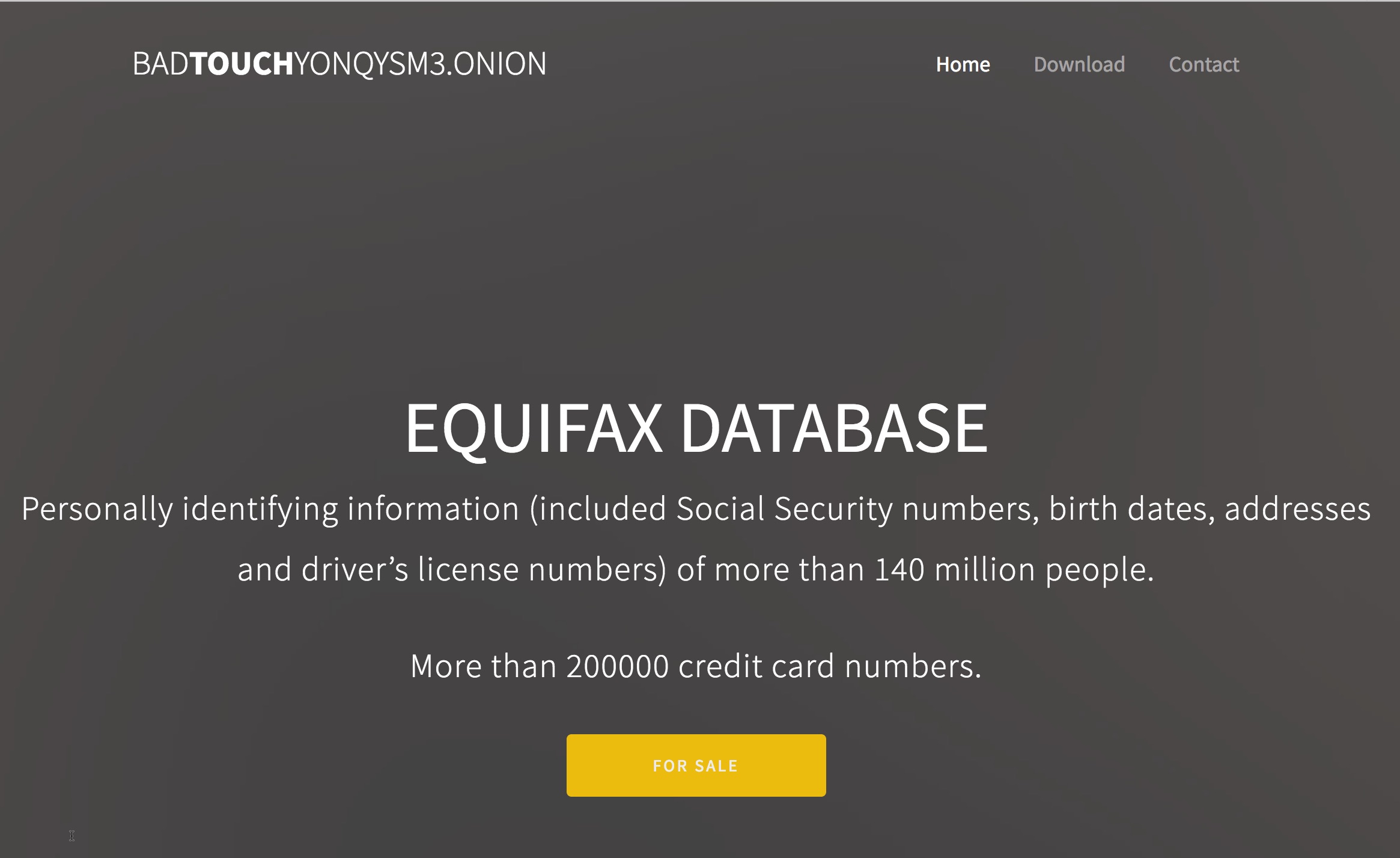
And so it begins. By this morning, there was already one potential class-action lawsuit against Equifax that had been announced, and at least two ads offering what is alleged to be hacked Equifax data for sale.

Indeed, things haven’t been going exactly swimmingly for Equifax since it announced its mega-breach that may impact up to 40% of all U.S. consumers. Their tool to help consumers figure out if they’re affected has been problematic on many levels, and security professionals immediately began taking Equifax to task for their incident response.
As bad as some of Equifax’s problems may seen already (their stock is down more than 13% at the time I am drafting this post), what could be even worse is if the hacked data actually find their way to a public dump.
Which brings us to the ads that appeared today.
An early listing, first reported by Catalin Cimpanu on Twitter, was from a self-described duo calling themselves “[email protected].” They explain their reasons on a site accessible via Tor:
We are two people trying to solve our lives and those of our families. We did not expect to get as much information as we did, nor do we want to affect any citizen. But we need to monetize the information as soon as possible. Every day that passes is worth less, and the limit will be on September 15th. That day all the information except the credit cards will be published. It’s a necessary damage for companies like Equifax to learn. If up to day 15 they pay the requested amount all the information and all the backups will be deleted. Our word may seem insufficient but we do not gain anything by posting personal information if it is not absolutely necessary.
They are asking 600 BTC by September 15, or say they will dump the database. Unlike the hackers involved in hacking HBO’s Game of Thrones, “Pasthole” do not indicate whether they had sent Equifax any extortion demands, and if so, what Equifax’s response had been, but their “reasons” suggest that there may have been a failed extortion demand. Equifax’s press release made no mention of any extortion or ransom demand, however.
The self-proclaimed hackers did not respond to an email inquiry sent by this site this morning that provided them with some data and asked them what they had in the database to go with it.
A second ad/listing, also seen on Twitter this morning, was from a hacker also known as “Revolver” or “@real_1x0123:”
#Equifax for sale #XMPP [email protected] pic.twitter.com/Cp7tAs4Xow
— 1×0123 (@real_1x0123) September 8, 2017
If you don’t recognize the alias, 1×0123 is the same hacker who claimed the PayAsUGym hack and who provided this site with verified proof of that hack.
But is he also responsible for the Equifax hack? A few hours later, 1×0123 tweeted:
#Equifax webshell, access to subdomains for sale
1 BTC #XMPP [email protected]— 1×0123 (@real_1x0123) September 8, 2017
Inspection of the the file directory he posted in the image file in his first tweet mentions the ayuda subddomain on Equifax and “ws0 4.1.3.”
Equifax did not immediately respond to inquiries sent to it this morning asking whether they could confirm or deny the accuracy of information @real_1x0123 had posted. The ayuda subdomain, which had returned content this morning, no longer returns any content.
This post will be updated if more information becomes available.