Paul Bischoff writes:
An online database of more than 5 million records apparently belonging to MedicareSupplement.com was left open and accessible to the public. On May 13, 2019, Comparitech worked alongside security researcher Bob Diachenko to uncover the publicly available MongoDB instance that appears to be part of the website’s marketing leads database.
MedicareSupplement.com is a US-based insurance marketing website that lets users find supplemental medical insurance available in their area. Users are required to enter personal information in order to get a quote.
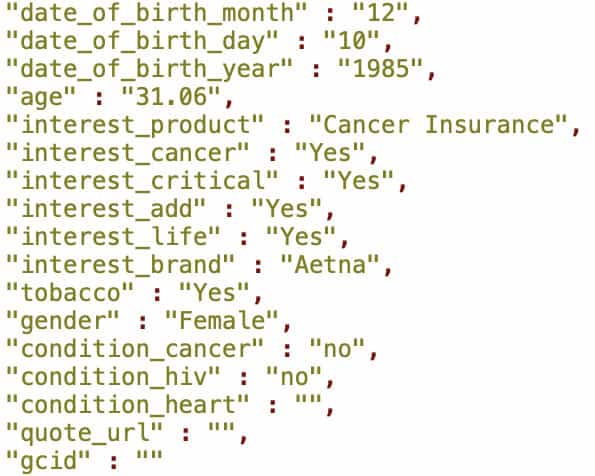
Of likely concern to those who try to protect health/medical data, the database included questions about consumer’s more specific conditions or interests in medical insurance. Bischoff reports that about 239,000 exposed records also indicated insurance interest area. A screenshot Comparitech published, reproduced below, shows that for the individual consumer in that record, their date of birth was provided, the fact that they were interested in cancer insurance and that was a critical interest, and we can see that their responses indicated that they are a female tobacco user who does not have cancer at the present time, nor HIV, nor a heart condition (or at least, that’s what they are telling the company).
Read more on Comparitech.