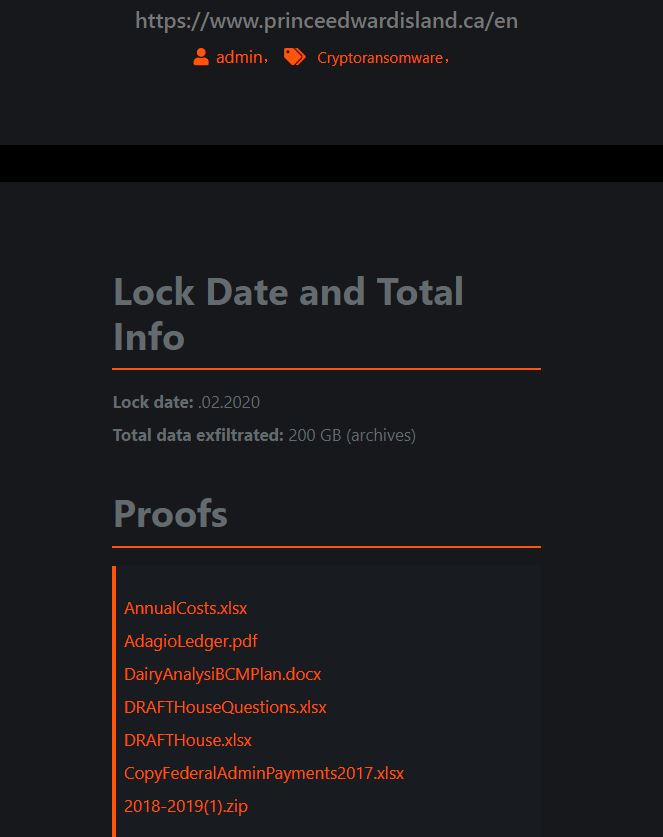
Earlier today, Maze Team added Prince Edward Island (PEI) to their website where they list victims who have refused to pay their ransom demands. As they have done in other cases, the attackers also provided some files that they exfiltrated as proof.
In looking into this attack, DataBreaches.net found that PEI had issued a statement on its site on February 25:
Islanders information protected as Government addresses malware discovery
On Sunday afternoon (February 23), Government discovered malware on its network, and extensive efforts continue to be taken to ensure Islanders’ personal information is protected.
Best practice measures to combat the malware were immediately put in place, and an extensive investigation is underway. Based on our investigation, there is currently no reason to believe that Islanders’ personal information has been affected by the malware.
Government services continue to be available without interruption, including payments to clients; however, Islanders may experience slower services for a few more days as efforts are ongoing to ensure the elimination of the malware and the continued safety of Islanders’ information.
As stewards of Islanders’ personal information, we felt that the public should be made aware of this discovery and reassured that security of their information is extremely important to the Government.
So far, then, there doesn’t seem to be any significant disruption in services, and kudos to PEI for being able to recover and keep services running. DataBreaches.net has reached out to PEI to ask them how much ransom was demanded, and to ask them to confirm whether any personal information was involved (although much of their data should be public record anyway). This post may be updated if a reply is received, but it appears that Maze Team is wasting its time trying to get any money from PEI.