Update 2: The attackers have confirmed that they had named the wrong bank and that the victim bank is Community Development Bank (in Minnesota).
UPDATE 1: Amanda Tavackoli SVP, Communication for TBK Bank has responded with the following statement:
I’m responding to your request for information regarding the DoppelPaymer claim.
Reports that CD Bank has been a target of ransomware are false. Our Information Security team and our core provider have conducted a thorough review and have found no evidence that CD Bank was compromised. The evidentiary documents are unrelated to CD Bank or any of its related entities.
At the present time, then, DataBreaches.net is not sure what is going on but with TBK/CDBank’s firm denial, this bears further inquiry. Stay tuned…
Previous post:
It’s getting uglier out there. Both Maze Team and the DoppelPaymer ransomware teams seem to be attempting to increase pressure on their victims by giving them less time to respond before their name and data get publicly revealed.
For its part, although Maze Team is clearly active and updating their site on a frequent, if not daily, basis, Maze Team has not replied to a number of queries this site has sent it about the removal of some victims’ names from their site and what that means. So far, only one of their HIPAA-covered victims seems to have reported their attack to HHS/OCR. DataBreaches.net is monitoring the situation to see if the other victims that Maze Team had identified to me in email eventually disclose publicly. Most of Maze Team’s victims have not replied at all to inquiries from this site asking them to confirm or deny the claimed hacks and none of the victims Maze Team identified to me that have not come forward have any notices on their websites, either. Ironically, perhaps, Crossroads Technologies, identified as a breached entity by Personal Touch Home Care as the source of their reported breach, does not have any notice on their website about the incident while it continues to advertise its security and help with HIPAA compliance.
Elsewhere, and as noted previously, DoppelPaymer attackers are experimenting with using the same kind of website naming and dumping approach.
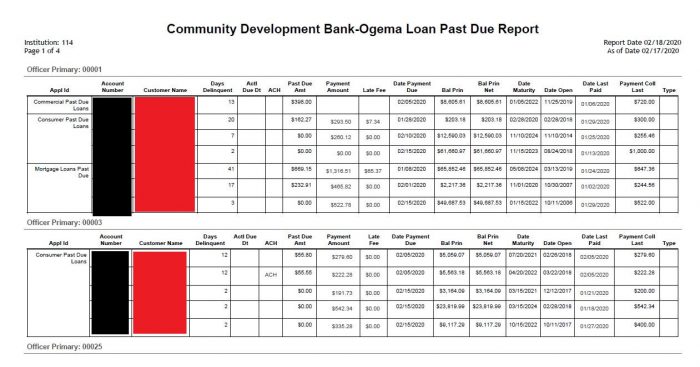
One of their targets appears to be CD Bank, the online division of Texas-based TBK Bank, SSB. NOTE: See the Updates at the top of this post. The victim bank is Community Development Bank, not CD Bank.
CD Bank has not responded to inquiries sent to it on February 27 and on February 28. An inquiry was also sent to TBK Bank today through their website. NOTE: They responded. See first update above this post.
In the interim, the attackers have dumped more of the bank’s data every day, with some files containing personal and financial information of bank customers, as the following redacted screencaps illustrate:

Neither the CD Bank nor the TBK Bank’s websites give any indication of anything amiss or any cyberattack, and as noted above, neither have confirmed nor refuted any claimed attack. NOTE: See updates. They were not attacked.
This post was edited several times post-publication to correct attributions and to keep readers apprised.