We know that no security is perfect, but when a company collecting and storing teenagers’ data has repeated breaches, it’s cause for concern – and possible investigation by federal and state regulators.
In 2017, we learned that the popular teen quiz app, Wishbone, had been “hacked.” According to reports at the time, hackers snagged 2.2 million email addresses and 287,000 cellphone numbers. It wasn’t really a hack, though, although media described it that way — it was a misconfigured MongoDB that someone found and downloaded.
In a statement to users at the time, the company wrote:
We value your privacy and deeply regret that this incident occurred. Maintaining the integrity of your personal information is extremely important to us. We sincerely apologize for any inconvenience this incident may have caused you. We are continuing to investigate this matter and have taken and will continue to take appropriate action to prevent future similar incidents. Please be assured that we will keep you informed of any developments in the investigation that may be of importance to you.
Now it appears that they were hacked once again in January of this year, and 40 million users’ data is now available on a popular forum.
On Wednesday, a well-regarded reseller on RaidForums first listed the database for sale.
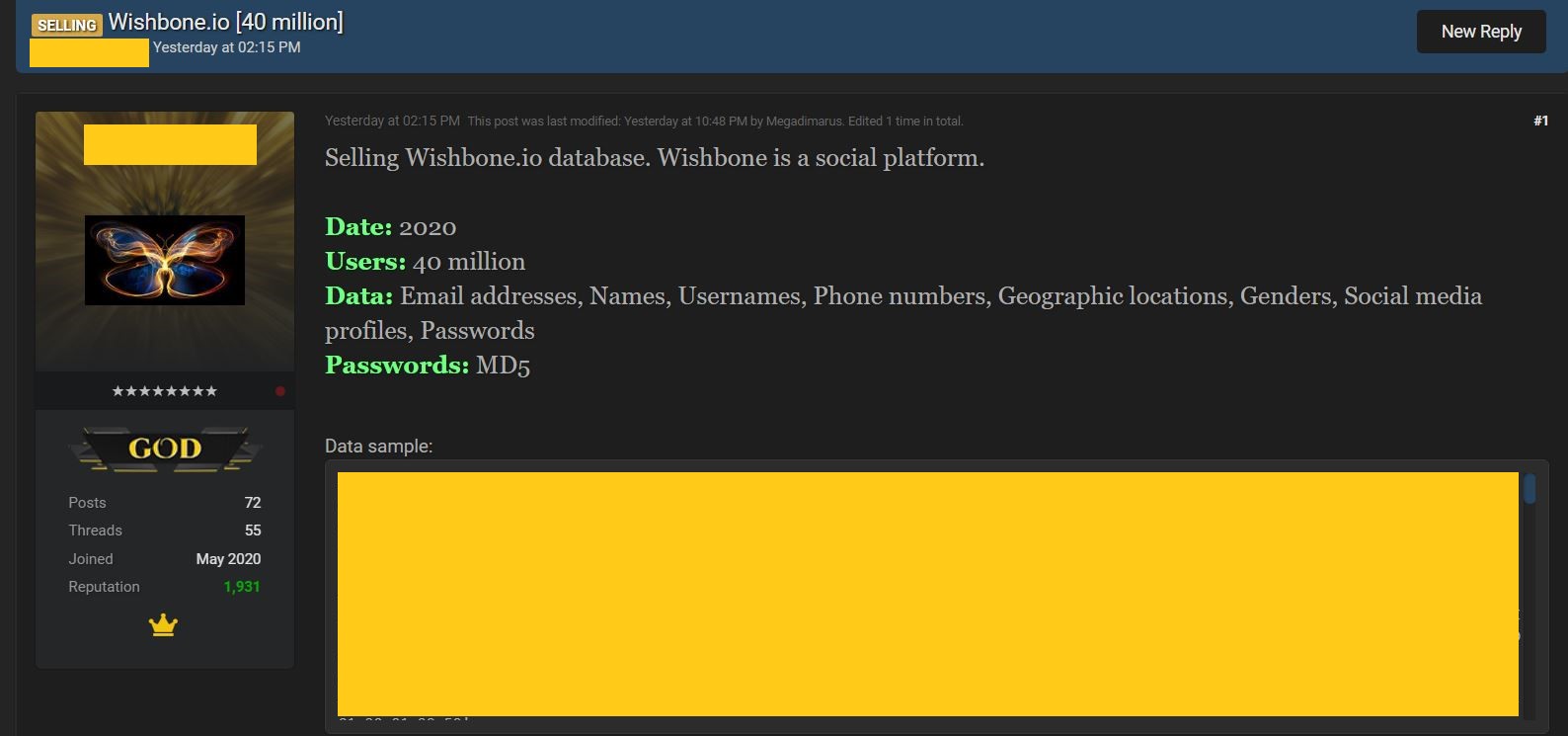
The data were described as containing 40 million users’ Email addresses, Names, Usernames, Phone numbers, Geographic locations, Genders, Social media profiles, and MD5 Passwords
ZDNet, who reported on the listing yesterday, noted that in verifying the data legitimacy, they also found links to teens’ photographs.
This morning, ShinyHunters, responded on RaidForums with their own listing:
Hello dear RaidForums community, since people are starting to resell wishbone, we’ve decided to leak it for free.
[“free” in the context of this forum, means the data are not being sold for cash or BTC, but for forum tokens].
The schema, as posted by ShinyHunters, includes:
uid,username,email,name,mobile_number,country_code, fbid,access_token,auth_token,ip,create_time,twitter_id,t witter_access_token,twitter_access_secret,gender,date_of_birth,password,image,follower_count,device_token, android_device_token,is_admin,timezone,displaying_post_date,is_device_active,shared_for_date, show_second_session_date,apple_idfa,google_advertiser_id,stickers_left, deleted_at,updated_at
And like the reseller listing it, ShinyHunters provided their own sample of the data. Both their sample and the reseller’s sample show that the data were downloaded in January 2020, even as late as January 27, 2020.
At the time of this posting, there is no indication on Wishbone’s site that they were aware of any hack. A request sent to their Media support contact resulted in an auto-reply that they would respond within 1 to 2 business days. Given that they told ZDNet yesterday that they were looking into things, it does not seem like they are yet in full crisis management or incident response mode, but a breach of this size and sensitivity is very concerning.
But meanwhile, back in the another-day-another-drama department, why did ShinyHunters just dump data that would likely have attracted a number of buyers? They say it was because others were already reselling it, but did they cut off their nose to spite their face? ShinyHunters responded to an inquiry from DataBreaches.net by saying that Whysodank (aka Whysodankk, ShinyHunter’s partner) had sold it to the reseller. But if you sell it to a known reseller why would you then screw the reseller by dumping the data for free? I put the question to ShinyHunters, who answered, “Well, let’s just say I didn’t agree with his decision.”
In a separate chat on Jabber, the reseller claims that they did not buy the data from whysodank, but were listing it for someone whysodank had sold it to:
“I was proxying the sale through a client. I guess he got angry I did that and he leaked it for free. Stupid move but what can you do”
With more data dumps and sales likely coming down the pike from ShinyHunters and whysodankk, that’s a question we may hear again.
This post was edited post-publication to restore some content that was accidentally deleted and to reformat the fields in the schema.
Update: Mammoth Media replied to my inquiry that contained a number of questions with this response:
Protecting data is of the utmost importance. We are investigating this matter and will share any significant developments.
As of the time of this update, there is still nothing posted on their web site, on AppStore, Google Play, or on their Twitter account to alert users that their data might be in unauthorized individuals’ hands. Also as of the time of this update, I’ve found that the Wishbone database has now also been listed on two Russian-language forums.