RagTrader reports:
Activewear retailer In Sport had its head office server and computers ransomwared in May, as cyber crime during COVID-19 escalates.
In a letter to customers, it revealed the attack was detected on May 16 but it was unknown what files hackers accessed.
Read more on RagTrader.
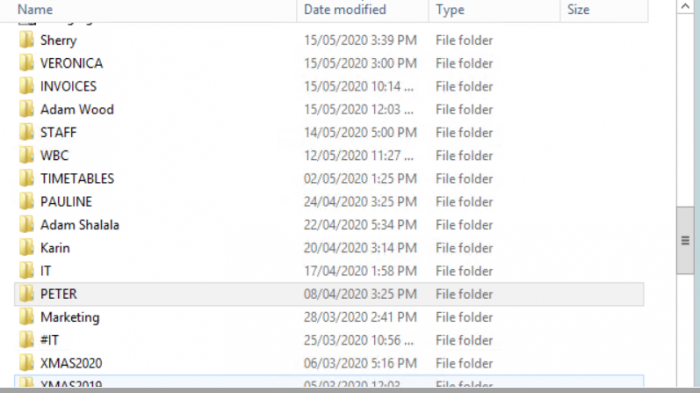
Update: This appears to be an attack by the Sodinokibi ransomware team (“REvil”). As proof, they dumped some data, most of which dealt with the costs and sales of various namebrand merchandise. Those files were subsequently removed by the hosting site where they had uploaded the data, although the data are now out there in various hands. REvil also uploaded a screenshot of a directory of some folders.