In a somewhat novel approach to ensuring that their victim knows they have been hacked and their systems locked up, the Egregor threat actors sent messages to some Cencosud stores.
Some video was shared on Twitter by @Irlenys:
El #ransomware que le pegó a Cencosud es #Egregor. La ransom note empezó a salir en las impresoras de varios locales de Argentina y Chile pic.twitter.com/k1Ps4IDUyq
— Irlenys (@Irlenys) November 15, 2020
Translation: The #ransomware that hit Cencosud is #Egregor . The ransom note began to appear in the printers of several stores in Argentina and Chile
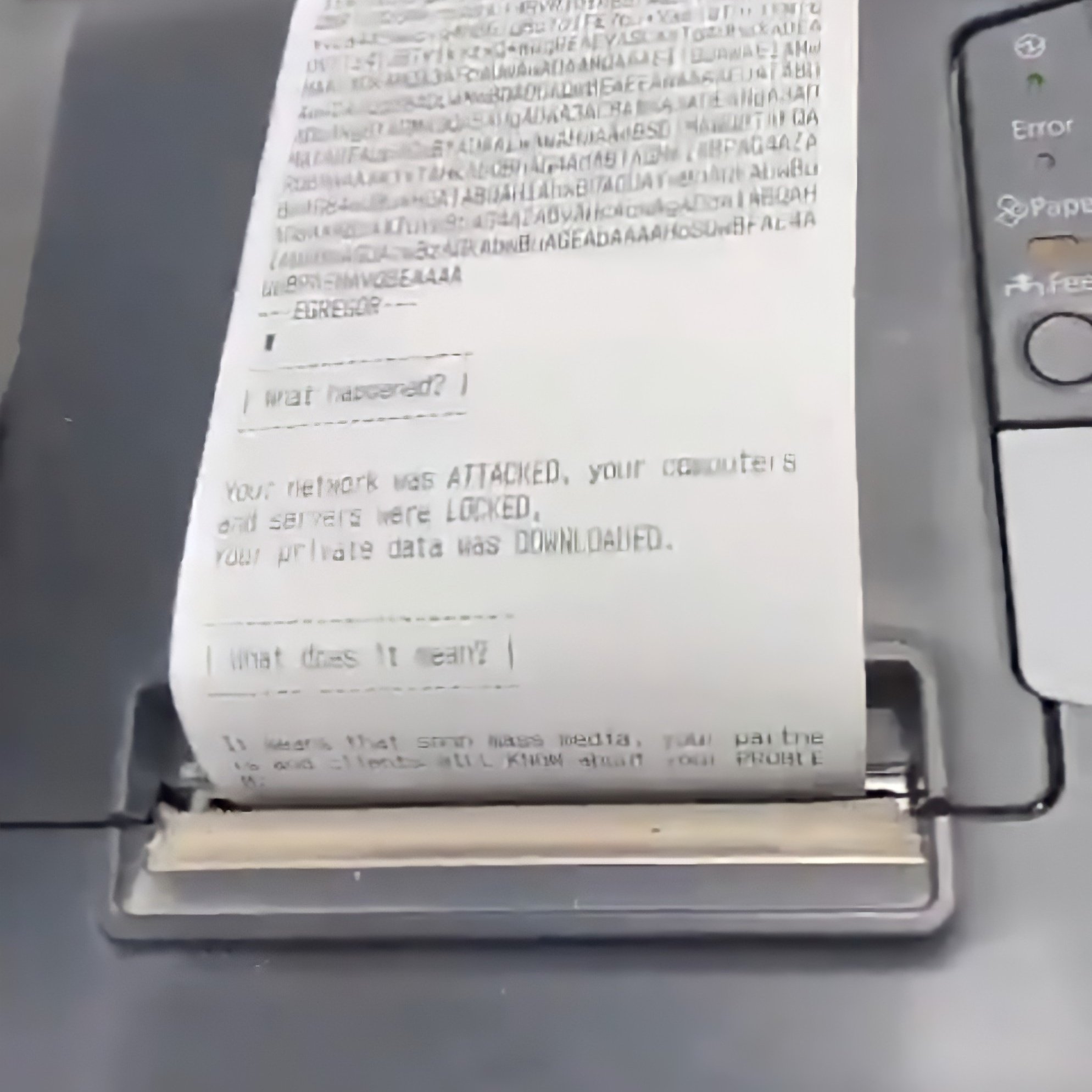
The ability to send ransom notes to printers is a feature of Egregor ransomware, as reported by BleepingComputer, who first reported on the Cencosud breach:
Clarín also reported that printers in numerous retail outlets in Chile and Argentina, such as Easy home goods stores, began printing out ransom notes as devices are encrypted.
This function is a known “feature” of the Egregor ransomware software, which will automatically print ransom notes to attached printers after the files on a device have been encrypted. For network-wide attacks, this could potentially lead to thousands of ransom notes being printed throughout the organization.