Over on AdvIntel, Tyler Combs has a post about threat actors attacking law firms. Many of us are already aware of a number of law firms who have been attacked and who have had their firm’s files dumped publicly when they refused to pay ransom demands, but if the biggest law firms fall prey, what does that predict for smaller firms?
Combs writes, in part:
Recent cases of cyberattacks against law firms illustrate the scale and ripple effects. For instance, in September 2020, one actor gained access to files containing I-9 employment authorization forms and was able to access the names, phone numbers, email addresses, dates of birth, Social Security numbers, and passport numbers of an undisclosed number of current and former employees of a law firm’s client; all information that could be used for identity theft. As part of its recovery from the attack, the law firm offered free credit monitoring services to all the affected customer’s employees – a costly and complicated process.
This case is not unique – the American Bar Association reveals that 29% of the respondents to a survey on law firm cybersecurity experienced breach-related threats in 2020, but only 34% of firms maintain cybersecurity incident response plans. It is therefore crucial for both firms and clients to have an accurate picture of the cyber threats facing the legal sector.
Combs provides more detailed examples of the type of threats law firms face, including have login credentials to their sites sold on the dark web to other threat actors who will exploit the access. “For example, since November 2020, AdvIntel has identified the RDP credentials of 17 law firms offered for sale in top-tier DarkWeb marketplaces,” Combs write.
RDP (Remote Desktop Protoxol) is one of the two most common ways threat actors gain access to their intended victim.
Read Combs’ entire article on AdvIntel, and if that doesn’t make your law firm take these threats more seriously, consider this:
 Jones Day, one of the largest international law firms in this country, has apparently become a victim of a ransomware attack, and some of their files — including confidential and sensitive files — have already been dumped publicly.
Jones Day, one of the largest international law firms in this country, has apparently become a victim of a ransomware attack, and some of their files — including confidential and sensitive files — have already been dumped publicly.
Jones Day was listed as having revenue of more than $2 billion in 2018. One of its practice areas is cybersecurity, and they have published a number of articles on their web site about ransomware attacks and how they have helped or advised clients how to respond to security incidents. They even publish a monthly privacy and cybersecurity newsletter.
What they do not seem to have published — at least not that this site has found — is any statement acknowledging that at least some of their files have been dumped by ransomware threat actors on the dark web.
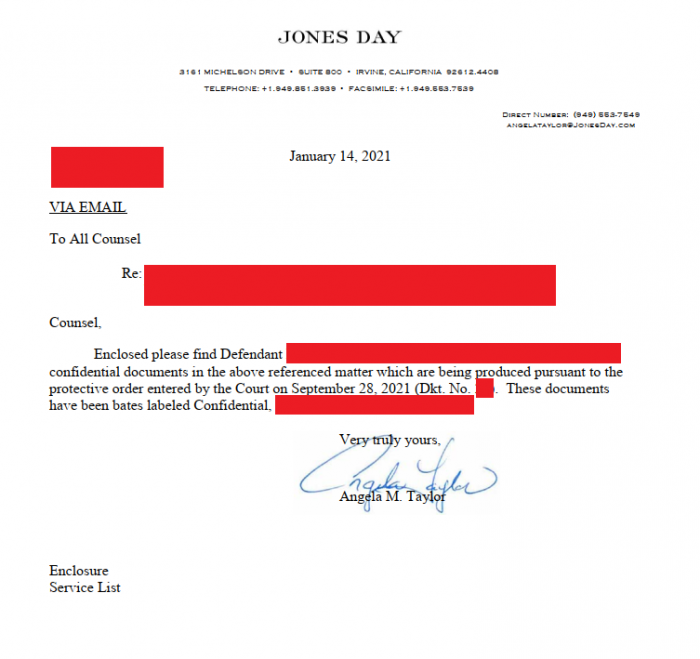
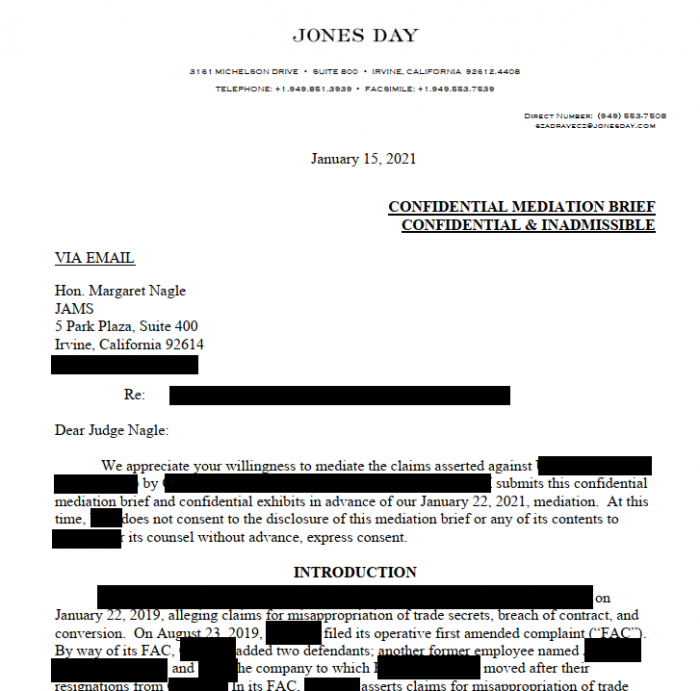
As proof of access, the threat actors known as CLOP initially posted some screenshots of files they appear to have exfiltrated. Two examples are provided below, redacted by DataBreaches.net. Both involve current and confidential communications.
When Jones Day did not respond to the increased pressure and threats, the threat actors appear to have dumped even more data.
DataBreaches.net sent an inquiry to Jones Day yesterday, but received no response. A second request was sent this morning, but also received no response. Nor is there any statement on their web site about any interrupted services or alerts. Although the law firm has neither confirmed nor denied the claimed attack, the files that this site inspected appeared to be from verifiable cases.
This post will be updated if a response or statement is received.
Update: Jones Day still hasn’t responded to inquiries, but the threat actors did, simply stating,
Hi, they ignore us so they will be published.
They subsequently added that they exfiltrated 100 GB of files (“70% zip and 7z files”).
DataBreaches.net will continue to try to get more information on this breach. In the past, Jones Day has recommended that breached firms notify clients promptly. One can only wonder if they are implementing their own advice right now.
Clarification: The threat actors subsequently told Vice that they did not encrypt the files — they merely stole (copies of) the data.