There is no notice of any cyberattack on the web site of Wolfe Eye Clinic in Iowa, but the clinic has been investigating and addressing an alleged attack for more than one month now while patient care continues at their multiple locations.
On April 1, threat actors known as Lorenz added the clinic to its relatively new dedicated leak site. Unlike some other dedicated leak sites that appear to just dump data to pressure victims into paying extortion demands, Lorenz has offered downloads for which interested parties — or the victim — can buy the key to open. The threat actors also seem to be offering to sell access to the clinic’s internal network.

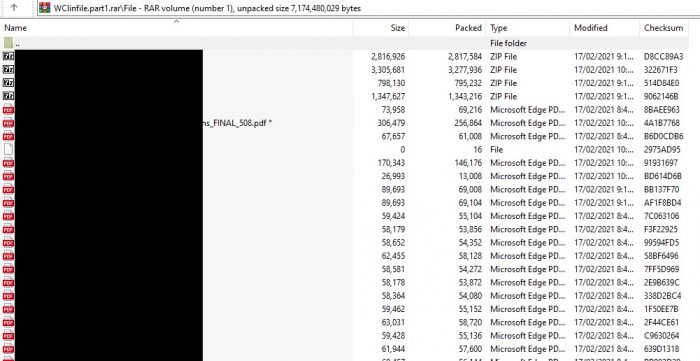
Lorenz did not post any proof of claim for Wolfe Clinic that can be accessed without a key or password, but it is possible to download the archives and see what contents are listed, as the redacted partial screencap below illustrates:
DataBreaches.net reached out to Wolfe Clinic, who provided the following statement:
The Wolfe Eye Clinic is aware of targeted efforts to access data on its systems. We are currently working with a team of forensic experts to fully understand the extent and implications of these incidents, which includes an earlier email phishing attempt.
While these types of situations have become all too common with health care providers nationwide, we recognize the significance of these events and quickly took the appropriate steps to address them once we became aware of their occurrence. Our comprehensive assessment is ongoing and may span a few more weeks. We are committed to sharing more information when it becomes available.
Wolfe Eye Clinic’s systems are fully operational, and our team has continued to provide high-quality patient care the entire time, whether it be an exam or surgical procedure. Likewise, we remain diligent against further intrusion efforts and are prepared to manage them accordingly.
The incident does not yet appear on HHS’s public breach tool, and it is not yet clear whether patient data was accessed or acquired. Nor has the clinic revealed whether their files were encrypted at all.
DataBreaches.net will provide updates if more details become available.
Updated June 22: AP has an update on this incident that states that the attack occurred on Feb. 8 and may have impacted as many as 500,000. Neither HHS nor those impacted appear to have been notified yet.