For a while yesterday afternoon, Vinny Troia of NightLion Security and DataViper.io appeared to lose control of tweets in his @VinnyTroia account.
After a number of tweets made it clear that @Pompompur_in was able to tweet from the account at will, Troia tweeted:
I am officially impressed and confused. There is no way someone hacked my @TwitterSupport @Twitter account… guessed a random password AND bypassed my MFA key? No way. So how are these tweets going out?
— Vinny Troia, PhD (@vinnytroia) May 16, 2021
I am officially impressed and confused. There is no way someone hacked my @TwitterSupport@Twitter account… guessed a random password AND bypassed my MFA key? No way. So how are these tweets going out?
With some hints from others to check for connected apps and a hint from Pompompurin himself, Troia did figure out that an API key to an old Twitter Dev app was used. But how did Pompompurin get that?
This morning, Troia publicly asked Pompompurin to be kind enough to share how he got the API and API secret keys.
Here’s the answer, courtesy of Pompompurin, who answered me when I asked him how he did it:
Look in the leaked WordPress dump of dataviper from when it was hacked
I found the Twitter api keys in there LOLOL
They’ve been sitting in there for like almost a year now without anybody noticing
That was how I did it
Came across it accidentally as well, had a folder of a few hundred random databases my friend sent me from his downloads folder & I recognized the file so I decided to just look through it real quick to see what was in it
(2455,’_wpdm_twitter_access_token’,’15708048-BReyv5yPqjKk9zeShlO4OrKZgtnR2WWpE9nem8Ky6′,’yes’),(2456,’_wpdm_twitter_access_token_secret’,’1B5iTT2nx07knrl4FqMhg7diBw5Elb2lvJHmcmfYYO3oc’,’yes’),(2457,’_wpdm_twitter_api_key’,’wALbz4iDdtP17SjECxU9aw’,’yes’),(2458,’_wpdm_twitter_api_secret’,’6v4QeYfYGZTHtvlzXDXNgzKaUSLQ1WBQI8h2GagB1A’,’yes’)
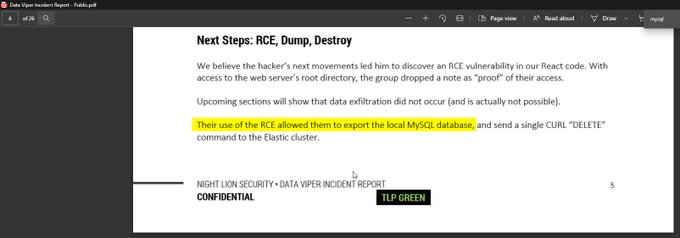
He mentions in his dataviper incident report, that the hackers weren’t even supposed to get access to the mysql databases, so I don’t think he would’ve intentionally planted those keys there
I am not including Pompompurin’s comments to me about this all, other than to note that it was not complimentary towards Troia’s cybersecurity skills.