The Sodinokibi (“REvil”) threat actors have added Betenbough Homes to their dark web leak site where they post files from victims who have not paid their extortion demands.
In the case of Betenbough, the attack was just added today to REvil’s site, but the breach occurred on May 3.
The most recent statement from the new home builder says:
Russian cybercriminals targeted and victimized local company, Betenbough Homes, resulting in a system breach on May 3. These criminals acted in a similar manner to those that held the Colonial Pipeline’s system for ransom and have attempted to strongarm Betenbough Homes with similar tactics.
In Colonial Pipeline’s case, the firm admitted paying DarkSide threat actors $4.4 million in ransom. Betenbough does not mention how much ransom REvil demanded or whether they are considering paying any ransom, but REvil is known to demand high amounts in some cases, with one of their core people, “UNKN,” having stated in a recent interview that he can never have too much money.
On May 15, Betenbough discovered that the criminals had been able to obtain some sensitive personal information of individuals from its system. In response, the firm reached out to notify individuals and offer them help like credit monitoring services.
“Our team knew the exact moment our systems were compromised, and we have been vigilant in how we have approached the remediation of this ransomware attack to protect each of our customers who have placed their trust in Betenbough Homes,” said Cal Zant, Betenbough Homes President. “We have consulted with cybersecurity experts who are monitoring this attack closely as well as legal professionals who are advising us on how to best care for potentially affected individuals.”
“Know that we will not allow these criminals to threaten our employees, customers or partners,” the firm added.
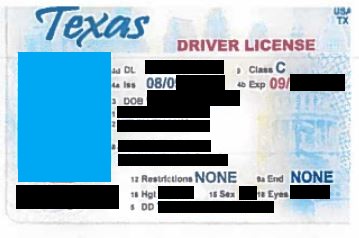
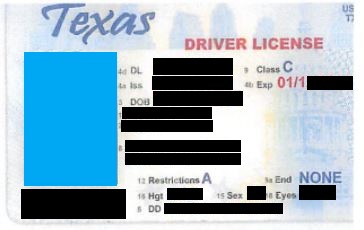
In in the interim, REvil has posted only a few images as proof of claims — images of driver’s licenses. The heavy redaction by our site indicates how many elements of personal information were exposed for each individual.
Editing and some content by Dissent