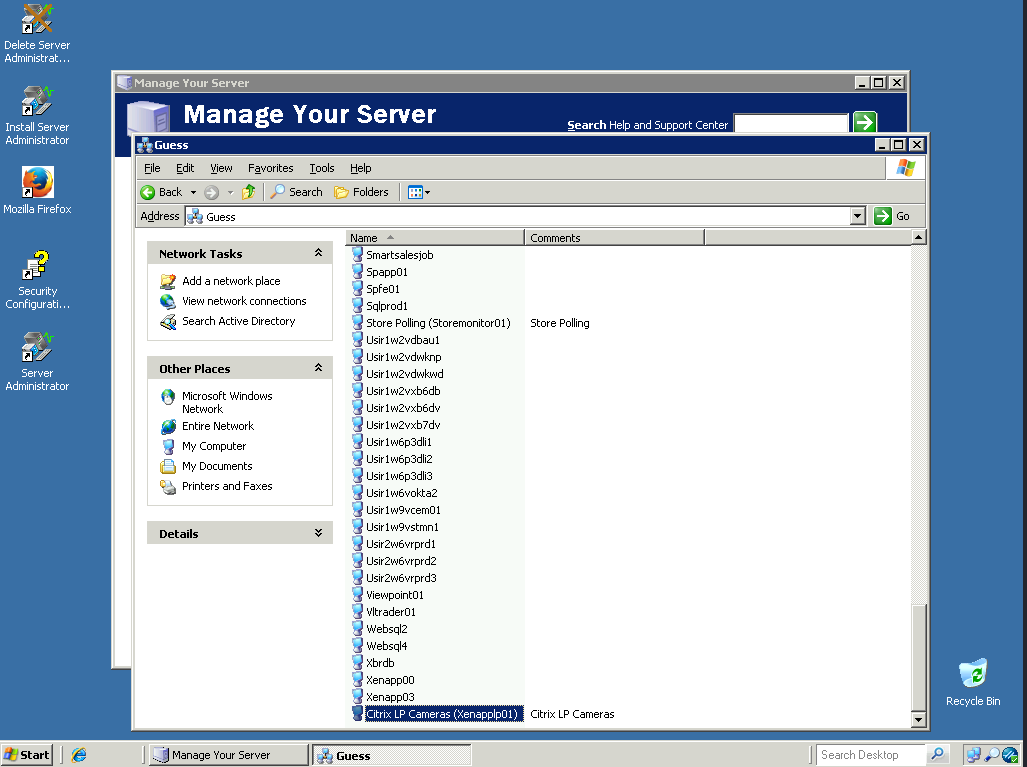
In April, DataBreaches.net reported a chat with DarkSide threat actors. As part of that report, this site noted that Guess, the well-known clothing and accessories retailer, had been attacked in February and listed on the DarkSide threat actor’s dedicated leak site.
DataBreaches.net had looked at the proof of claim that DarkSide had posted and described the claims concerning 200 GB of data, but did not post any of the screencaps or proof of claim at that time.

Weeks after the interview with DarkSide, DarkSide folded in the wake of the Colonial Pipeline attack and ransom payment, noting that they had lost access to parts of their own infrastructure and that funds from the payment server (theirs and clients’) had been withdrawn to an unknown address.
At the time they disappeared, Guess was still listed on their leak site but without any major data dump, suggesting that: (1) Guess had not paid ransom, and (2) DarkSide was still giving it some time before giving up on them.
But then what happened to the 200 GB of Guess data that DarkSide claimed to have exfiltrated? Is it in the hands of an affiliate? Was it on a server that got seized? At the time that they shuttered operations, DarkSide had issued a statement saying that it would hand over its decryption tools to affiliates, giving those who had worked with them on particular attacks the ability to negotiate ransoms with those victims directly.
“You will be given decryption tools for all the companies that haven’t paid yet,” the statement read. “After that, you will be free to communicate with them wherever you want in any way you want.”
So did some affiliate get the keys to Guess’s data?
There is much we do not know yet, but this week Guess filed a notification with the Maine Attorney General’s Office and started notifying individuals.

The Notification
In their notification to Maine, Guess’s external counsel reported that the breach occurred between February 2 – February 23 and impacted 1,304 individuals. The notification stated:
On May 26, 2021, the investigation determined that personal information related to certain individuals may have been accessed or acquired by an unauthorized actor. The investigation determined that Social Security numbers, driver’s license numbers, passport numbers and/or financial account numbers may have been accessed or acquired.
Guess began mailing notifications on July 9, explaining that it had taken time from May 26 to find contact addresses for all those who needed to be notified. Those notified are being offered a complimentary one-year membership in credit monitoring and identity theft protection services through Experian.
Guess’s notification to the state and to the individuals makes no mention of DarkSide, any affiliate, or any ransom demand. DataBreaches.net emailed an inquiry to Guess about what happened after DarkSide disappeared, but no reply was immediately provided. This post will be updated if a reply is received.