On June 20, DataBreaches.net reported that The Woodruff Institute in Florida had been attacked by “Grief” threat actors. At that time, the threat actors had dumped some files concerning business operations from the multi-location plastic surgery and dermatology practice, but other than about 50 laboratory test result reports for patients, there was not a tremendous number of files with protected health information in the dump.
Since that time, the threat actors have dumped more files.

The newly added files are in folders called “Refund Request Letters“, “Medics“, and “Secondary.” The threat actors also posted a list of all of the practice’s machines (120).
In the folder called Medics, there are subfolders from 2016 to 2021, with xlsx files organized by month within each year. We did not calculate the number of unique patients, but as just one example: one 2021 spread sheet for just one month contained almost 1500 records, with the following data; Patient name, MRN (Medical Record Number), A/R (Insurer), Policy Number, Date of Service, Procedure Code, Balance Due, Provider, Date, Collector Notes.

That month’s records involved approximately 700 unique patients, and that was just one month.
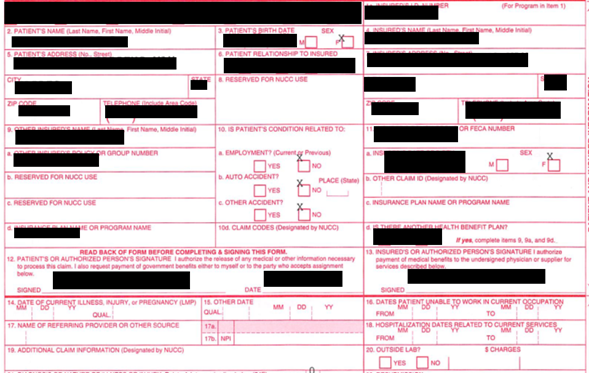
The folder called “Secondary” contained health insurance claim forms with the standard data fields used in such forms: patient name, birth date, patient address, ID number insurance, telephone number, city, plan name, diagnostic code, and treatment code.
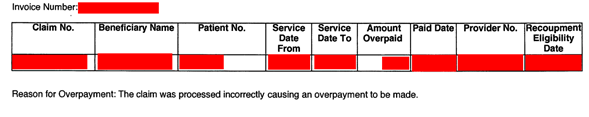
The third folder, “Refund Request Letters“, consisted of subfolders for 2018-2021. The 2021 one contained more than 200 files, where the requests contained data fields like Claim No., Beneficiary Name, Patient No, Service date from, Service date to, Amount Overpaid, Paid date, Provider No., etc.
DataBreaches.net reached out to the Woodruff Institute several times, the last time being July 6, but no response has ever been received. The incident has not (yet) appeared on HHS’s public breach tool, and there is no notice on their web site at this time. So we do not know whether they have notified HHS, whether they have notified patients, and if so, how many, were their files encrypted, and if so, did they suffer any medical records loss or corruption?
At some point, we expect that they will issue a press release or notice, and this post may be updated at that time.
Update: Post-publication, the threat actors dumped additional records that included more than 50 narratives of patient complaints and the staff’s responses to the complaints. Most of the complaints appeared to be from 2018.
Reporting by Chum1ng0; editing by Dissent