Catalin Cimpanu reports:
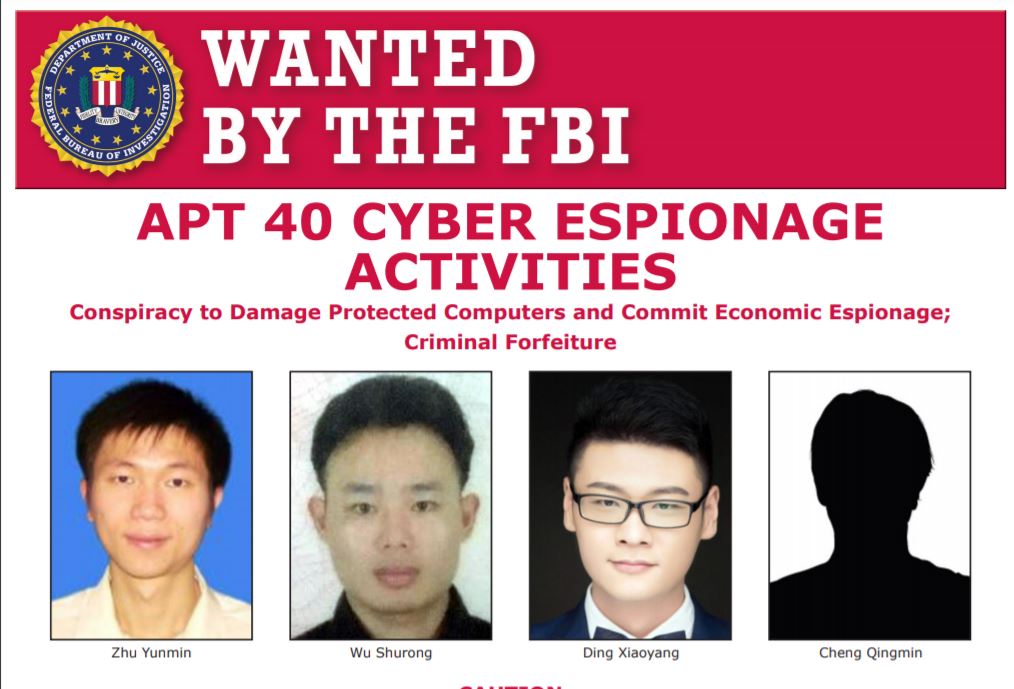
The US Department of Justice has indicted four Chinese nationals today for hacking companies, government agencies, and universities across the world on behalf of the Chinese government.
The US said the four suspects, believed to be part of a much larger group, set up a company named Hainan Xiandun Technology Development Co., Ltd. (海南仙盾) (Hainan Xiandun), which they used as a front for their hacking campaigns.
US investigators said the company operated under the direct supervision of the Hainan State Security Department (HSSD), the provincial arm of China’s Ministry of State Security (MSS).
Read more on The Record.
Related: