The following is all machine translation of a notice from CERT-RO (Romania)
SRI, in cooperation with CERT-RO and the Clinical Hospital No.1 CF Witting in Bucharest, recently investigated a cyber attack with the ransomware application PHOBOS, which targeted the entity’s servers in the field of health.
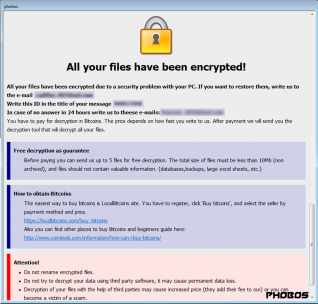
Following the encryption of the data, the attackers requested the payment of a ransom for their decryption, a payment that was not made by the affected institution. However, the current activity of the hospital has not been interrupted, continuity being ensured through the use of offline registers.
Moreover, the present attack is similar to the one in the summer of 2019, when 4 other hospitals in Romania were affected by PHOBOS, in the context of the lack of antivirus solutions at the level of the IT&C infrastructure used by them. PHOBOS ransomware has a medium level of complexity, using as a method of infection, mainly Remote Desktop Protocol (RDP) connections.
Since the beginning of the pandemic in 2020, CERT-RO and cyber security experts from the Cyber Volunteers 19 – Romania group have carried out joint warning and awareness campaigns dedicated to the medical units in the country. The main purpose of this initiative is to prevent, identify and properly address possible IT vulnerabilities of health care providers before it is too late.
The recommendations offered in this approach to support the medical environment are sometimes applied quickly and appropriately. But there are also cases where, for various reasons, the necessary security measures are not applied in time.
In order to prevent ransomware attacks, the experts of the CYBERINT and CERT-RO National Center recommend the rapid implementation of security policies and measures such as:
- Using an updated antivirus solution;
- Disable RDP service on all stations and servers in the network;
- Update operating systems and all applications used;
- Frequent change of passwords of all users, respecting the recommendations of complexity;
- Periodic verification of all registered users, to identify new users, added illegally;
- Backing up critical data on offline data carriers;
- Keep encrypted data in the event that an decryption application may appear in the online environment.
h/t, @Metacurity