It’s bad enough experiencing one ransomware attack. Imagine experiencing two, because that’s what Episcopal Retirement Services (ERS) in Ohio has been dealing with.
On or about September 24, ERS discovered that i had been the victim of what it describes as a cyberattack that impacted its systems and servers. Then on October 22, they experienced what they describe as another incident that was determined to be a ransomware incident.
At this time, ERS also learned that the September incident was a ransomware attack.
ERS’s investigation is ongoing, and their external counsel reports that ERS has not determined how its systems were accessed.
The notification by Whiteford, Taylor, & Preston LLP to the Maine Attorney General’s office does not indicate what type or types of ransomware were involved, or what any ransom demands might have been. Nor has ERS shown up on any dedicated leak site where threat actors might disclose their attacks.
The incident(s) resulted in the exposure and potential acquisition of protected health information (PHI). While the types of PHI vary by individual, it could include first and last names, addresses, gender, social security numbers, phone numbers, and dates of birth. The information potentially impacted also may have included medical diagnoses, health care provider name, insurance numbers, and Medicare number.
ERS plans to notify 4,133 patients, but since the investigation is ongoing, the number may change.
Additional information is included in the notice on their website.
Updated Nov. 23: @DF_CyberGuy on Twitter helpfully pointed out to me that on Oct. 23, one day after the second ransomware attack, Groove threat actor(s) posted ERS on their site.
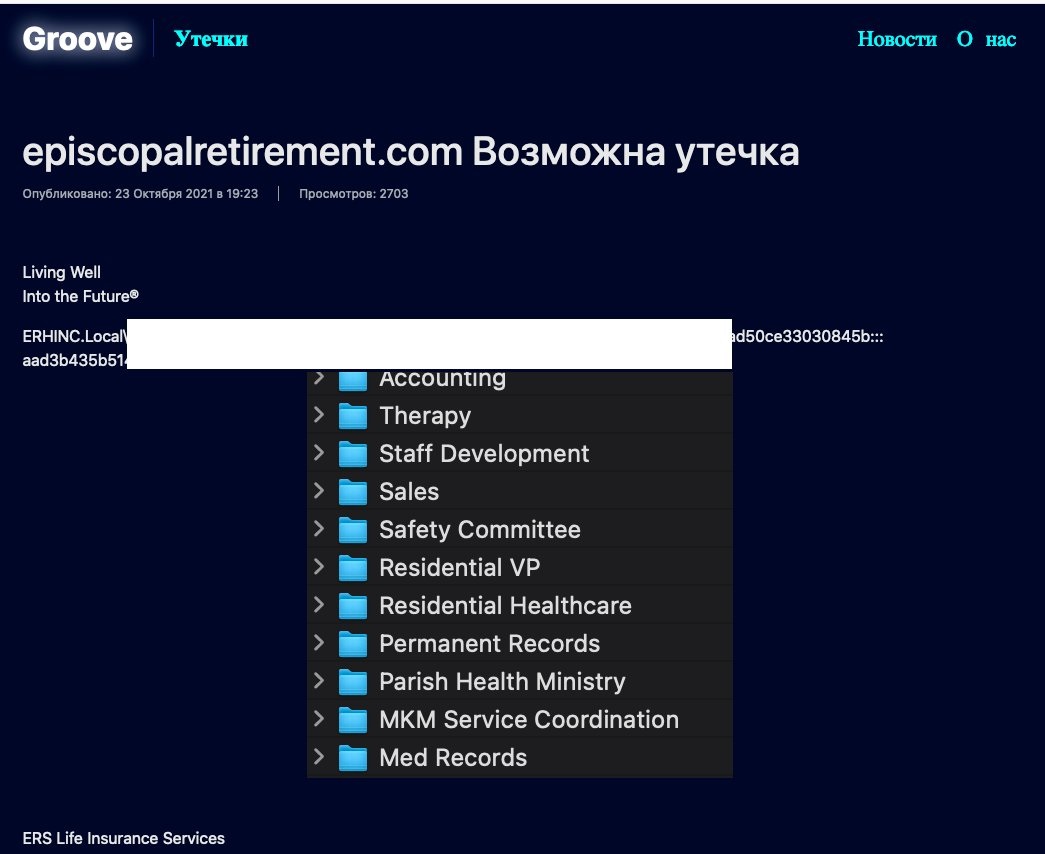
Whether Groove was responsible for the attack or was just listing data for other(s) is unclear, as Groove recently claimed that their whole purpose in creating their site was just to embarrass the media. Most in the media did not believe the claim and believe that Groove just failed so miserably as a threat actor that they made up some silly explanation. Because the site is gone now, however, we have no follow up on why ERS wound up on that leak site or who else might have the data.