Update of February 24, 2022: Jacksonville Spine Center, P.A. (JAX Spine and Pain Centers) reported a hacking incident to HHS on February 10 — the same date that this site first reported on claims by Avos Locker to have acquired data on 260,000 patients. JAX never responded to this site’s inquiries, but seems to have reported to HHS that 38,000 patients were impacted or notified. That’s a big difference between what Avos Locker claimed and what the covered entity reported.
DataBreaches.net has since found a statement on JAX’s site that says that the attack occurred on January 24. The statement stresses that only data prior to May 2018 was involved, and no clinical data was involved — only demographic data (which is what this site had noted in the original post).
Original post:
Covered entities in the medical sector continue to be an attractive target for ransomware groups, and earlier this week, Avos Locker added Jax Spine and Pain Centers (“JAX”) to their leak site. JAX has seven locations in North Florida and south Georgia.
According to the threat actors’ listing on their dark web site, “We have the full EHR (Electronic Medical Records) database for 262,000 patients! We are publishing list only for first 100 patients as proof.”
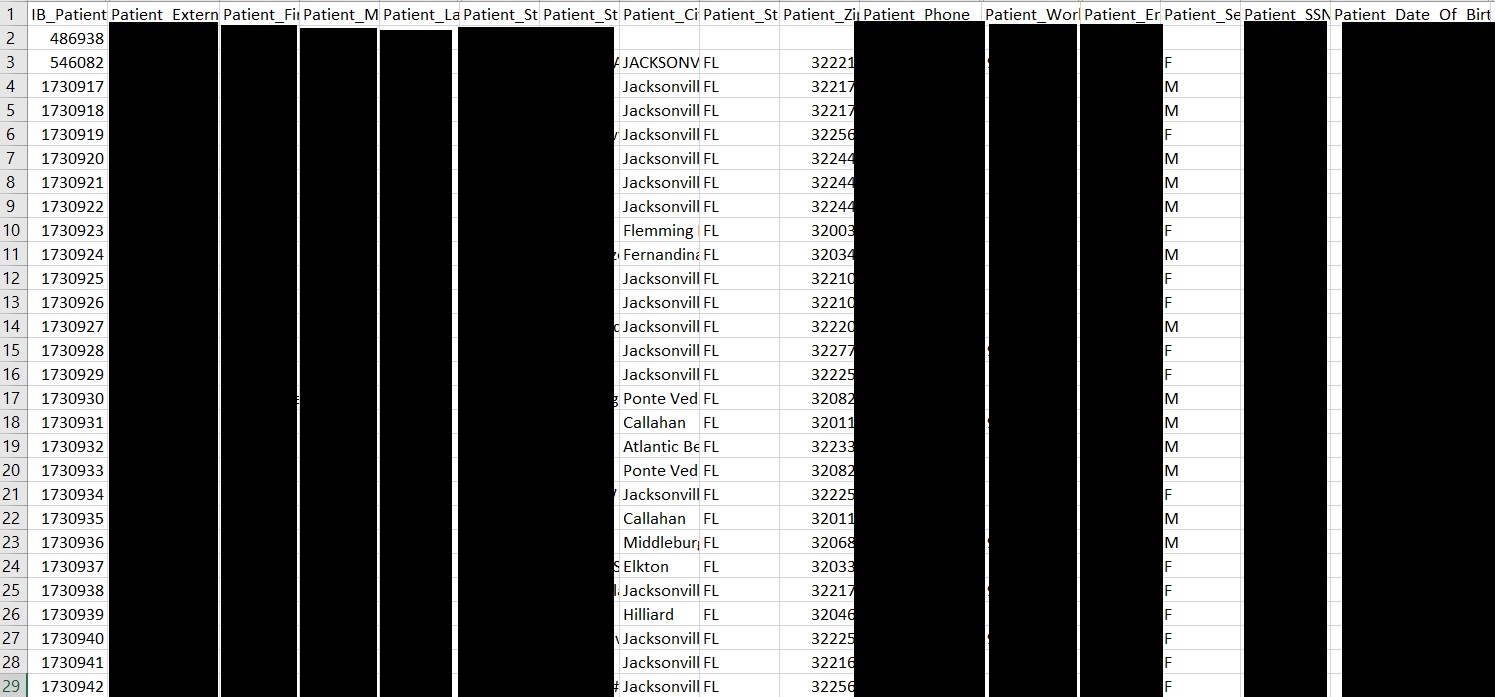
DataBreaches.net examined the .csv file with 100 records and found that it contained what appeared to be older data (circa 2012-2017) with demographic information fields that included patients’ first and last names with middle initial, postal address with zip code, email address, home and work phone numbers, date of birth, Social Security numbers, and some information on payment guarantor and provider. Patient ID numbers were also incorporated, The 100 records did not represent 100 unique patients, as there were multiple records for some of the names and Patient ID numbers.
There was no sensitive medical information in this particular sample such as diagnosis, treatment codes, dates of service, or specific health insurance information.
According to an Avos Locker spokesperson, all the files they acquired — which they claim is the full EHR database — are in text format. There are reportedly no pdf files or image files.
Attempts to validate the data were impacted by the age of the data. Sampling from the records, DataBreaches.net was able to find individuals of the right age (or now deceased) from Florida but in some cases, the individuals could not currently be found at the street address in the .csv file (they had likely moved over time). Attempts to validate the SSN data found valid SSN numbers that corresponded to varying degrees with the patient’s reported date of birth. In some cases, there were discrepancies between the date a particular SSN was issued and the patient’s reported date of birth although the SSN number was a valid number.
Based on validation attempts so far, the data look real, and even if there are no medical diagnoses and other types of data, this would be a reportable breach under HIPAA/HITECH. Avos claims that they do have the other data types, but have not (yet) provided this site with any hard proof of that.
Significantly — for JAX — an Avos spokesperson states that Avos did not lock/encrypt the EHR database and confined themselves to exfiltrating a copy of it.
JAX was allegedly notified by Avos via numerous calls, but allegedly did not respond and has not attempted to negotiate with the threat actors at all, according to the Avos spokesperson. They have not revealed when they first accessed JAX’s system.
DataBreaches.net has sent JAX’s owner, John Carey, and a physician partner, Dr. Michael Hanes, two emails over the past 24 hours requesting that they confirm or refute the claimed attack and to answer some questions about the incident. The questions included whether data from patients at all of their locations had been stolen, whether they could confirm that files with diagnoses and insurance information had been stolen, whether any employee or contractor information had been stolen, and whether they have already notified HHS, patients, and regulators if required by law.
There has been no response at all, and there does not seem to be any notice on their website.
This post may be updated as more information becomes available.