On June 1, Clarin reported that their Artear (Arte Radiotelevisivo Argentino) group, had been attacked by cybercriminals who managed to install ransomware. Artear is responsible for producing and broadcasting several television channels in Argentina.
Clarin’s announcement did not name the threat actors, and claimed that by then, no ransom demand had been received, but DataBreaches received a tip, now confirmed, that it was the Hive group that attacked them.
“Artear.com, Downloaded most important information with a total size over 1.4Tb,” a spokesperson for Hive informed DataBreaches on June 18, adding they exfiltrated:
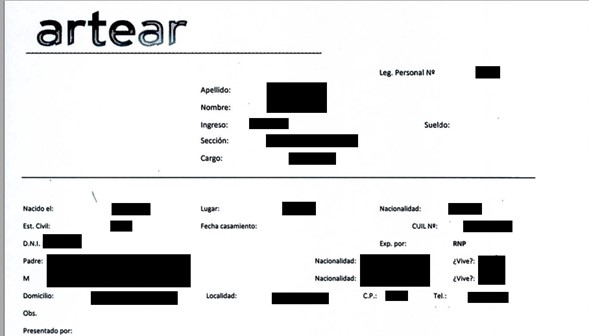
contracts, nda and other agreements documents, company private info (budgets, plans, investments, company bank,statements, etc.)executives info (DNI and CUIT numbers, insurances, vehicles, emails, addresses, phone numbers, payments, working hours, etc.) employees info (DNI and CUIT numbers, insurances, emails, addresses, phone numbers, payments, working hours, etc.)
DataBreaches was provided with a file tree and an extensive sample of files that appeared to come from Artear. The sample contained invoices, employee contracts, health insurance-related information, affidavits, some passports, ID cards, and medical examinations.

DataBreaches sent an email inquiry to Artear to ask them whether they had received any ransom demand from Hive and whether they had notified any employees.
Not receiving any reply from Artear, we asked Hive’s spokesperson about when they made any demand of Artear. The spokesperson responded:
They didn’t contact us to get a demand, We sent several emails to top managers and got no reply
The attack took place on June 1st. All systems were encrypted
It was not just the systems that were encrypted, the spokesperson claimed.
All backups were encrypted. May be they have offline backups but we don’t think so
As of June 20, when we inquired, Hive’s spokesperson claimed that they still had access to Artear’s system.
Earlier today, Hive added Artear to their dark web leak site. The listing notes that files were encrypted on June 1.

The listing also provides two links to data. One link appears to link to data with Human Resources files while the other link has one person’s name as the directory name. Both links have returned 504 Gateway Time-Out messages today whenever we have attempted to connect to those urls, so DataBreaches does not know what files might have been uploaded.
This post will be updated when more information becomes available.