Oh what a tangled web we weave….
Back in October, DataBreaches reported that Snatch Team had listed Kenosha Unified School District in Wisconsin on its dedicated leak site. By the end of the day, however, the listing had been removed without any data having been leaked.
Then in November, REvil listed KUSD on their leak site, and without any fanfare or commentary, leaked data. In response to an inquiry from DataBreaches, KUSD noted that they had disclosed a ransomware attack in September and had notified employees after an investigation determined that employee data might have been acquired.
And that’s where things remained until this week when Snatch Team re-listed KUSD on their leak site and dumped data — exactly the same data that REvil had leaked.

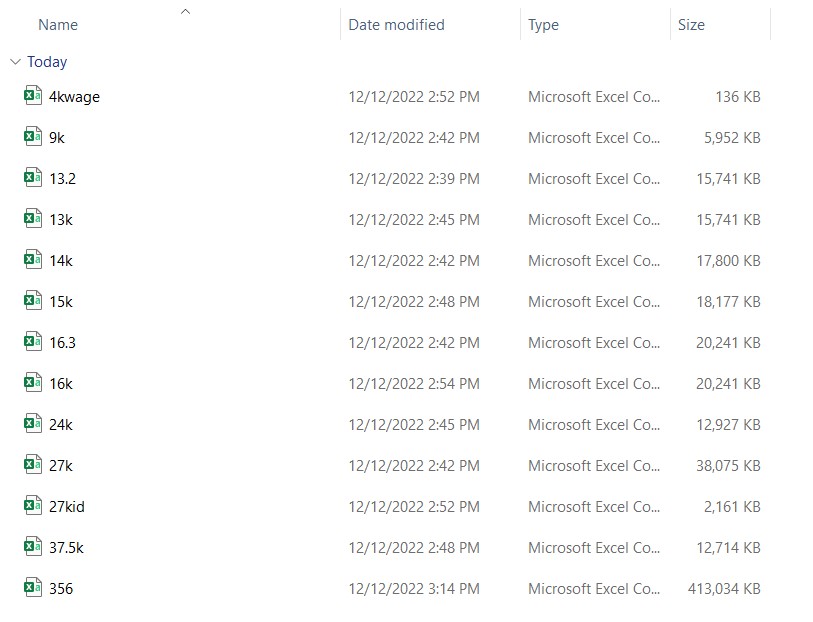
The files, relating to personnel, are identical.
DataBreaches reached out to Snatch Team on November 29 to ask them about the fact that REvil had leaked data from KUSD and whether both teams had collaborated somehow. Snatch’s spokesperson responded yesterday:
We have nothing to do with Revil or any other. Based on our experience, if a company does not feel responsible to its customers for the safety of confidential information, it will lose it again and again and pretend that nothing happened.
But given that Snatch leaked data from KUSD yesterday and it’s the exact same data that REvil had leaked, DataBreaches responded:
It’s just amazing that you and REvil were both in KUSD in September? And both exfiltrated exactly the same folders and no other data? And then REvil locked them, which means you had already exfiltrated before REvil deployed the locker. How did your groups not trip over each other in there? Wild coincidence…
And that’s where I think we’ll have to leave this one for now because it sounds like some affiliate may have worked with both groups or someone sold the same access to both groups around the same time. In any event, KUSD has notified those it knows was affected.