On April 23, the BianLian ransomware group listed:
A***** *** * ******* S*******
BianLian often uses the asterisk system before they actually name the victim and leak data.
Today, though, DataBreaches also saw the following on the RansomHouse leak site:
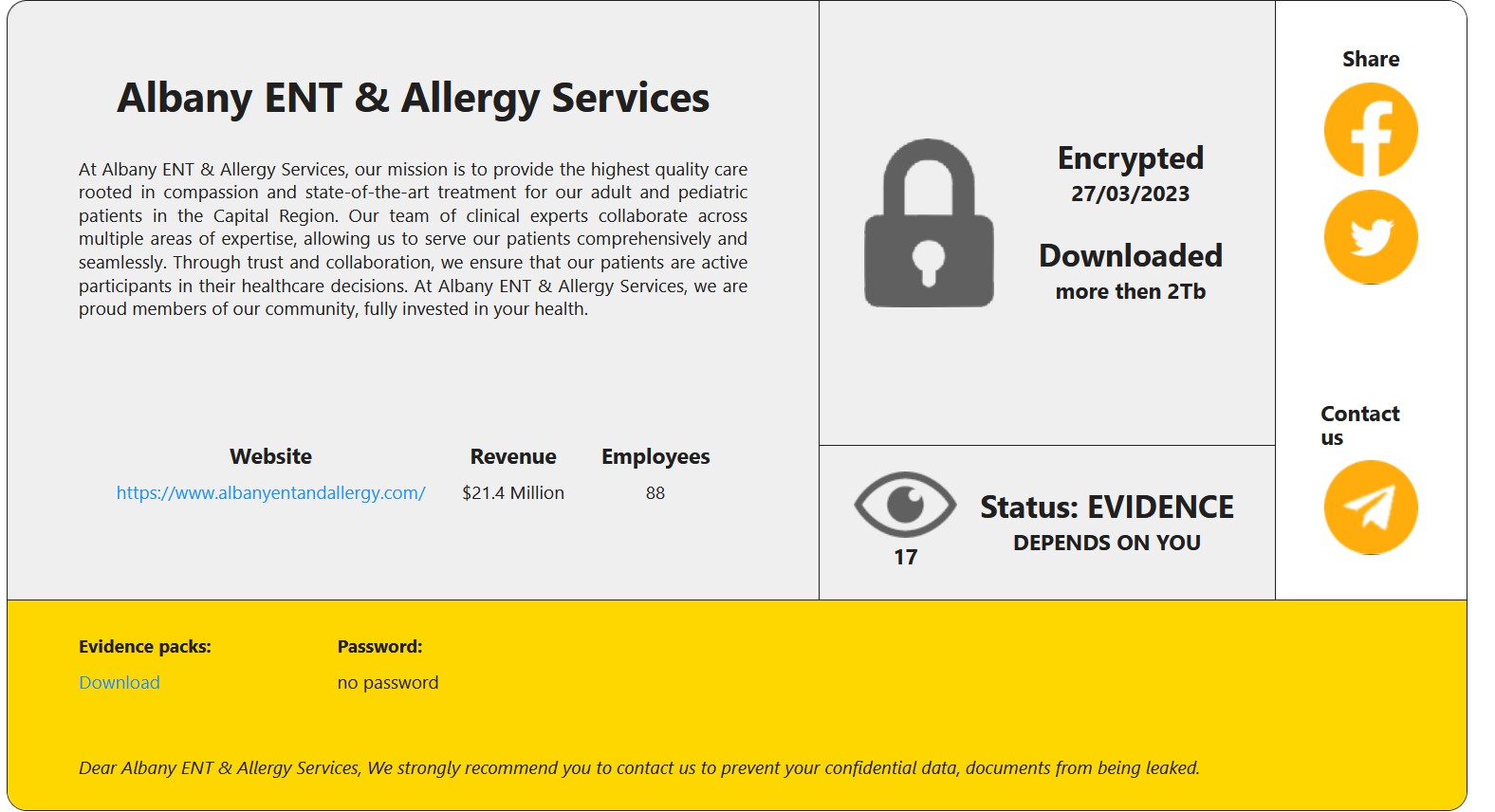
Albany ENT & Allergy Services
They’re both listing the same entity (even the listed revenues are almost an exact match), but only RansomHouse has posted a proof pack at this point. They claim to have locked the victim on March 27 and to have downloaded more than 2 TB of files.
So when did BianLian lock the victim, if they did? Are there two sets of extensions, or did only one group lock the victim?

Albany ENT & Allergy Services’ web site showed 404 for the home page content earlier today but appears to have been restored by now. Nothing on their website indicates that there has been any data security breach.
DataBreaches has left an inquiry for BianLian on their QTox account, but no reply was immediately available. This post will be updated if a reply is received.