Update of May 6: Although neither the clinic nor the attackers have confirmed it yet, this attack appears to be the work of BianLian, whose obfuscated description on their leak site matches Murfreesboro’s description. BianLian claims to have over 250 GB of files.
Carmyn Gutierrez and Caleb Wethington report:
The Murfreesboro Medical Clinic & SurgiCenter was the victim of a sophisticated criminal cyberattack, according to a press release.
The cyberattack happened on April 22 and in response, MMC says they had to shut down all operations on May 1-3 to limit the spread of the attack. Since shutting down, they’ve been working with law enforcement and experts to identify the source and scope of the attack in order to restore normal operations.
Read more at WMSV.
The text of the clinic’s statement of May 2:
Murfreesboro Medical Clinic & SurgiCenter Faces Critical Infrastructure Attack
MURFREESBORO, TENN. (MAY 2, 2023) – On April 22, 2023, Murfreesboro Medical Clinic & SurgiCenter (“MMC”) was the victim of a sophisticated criminal cyberattack. In response, we rapidly initiated an emergency shut down of our network to limit the spread of the attack within our systems and those of our technology partners. Since that time, we have been working with law enforcement agencies and third-party experts to identify the source and scope of the attack in order to restore normal clinic operations. Our first priority was to contain the incident and protect our patients and employees.
In conjunction with law enforcement, we continue to investigate the incident while also taking action on our infrastructure to, hopefully, prevent any further attacks. With the quick detection by our technology experts, we believe we have been able to limit the impact of this criminal attack. We are currently in the process of restoring our systems safely with enhanced security features and controls. While that process is being undertaken, MMC has closed all operations and hopes to open on a limited basis on Wednesday, May 3rd, with the rest of our operations coming online shortly thereafter.*
Joey Peay, CEO of MMC, states: “Preserving sensitive patient and employee information is of the utmost importance to MMC, but like so many other organizations around the country and despite its best efforts, MMC has found itself as the target of criminals attempting to steal personal or company data. I want to thank our patients and employees for their understanding and patience while we work to make sure our computer infrastructure is secure and free of any harmful software.”
We have worked diligently to communicate closures with all patients in a timely manner using all methods of communication at our disposal. Future updates regarding clinic operations will be posted to our website, social media platforms, and through emails and phone calls directly to patients. We apologize for the vagueness of our recent communications, but we did not want to do anything that would impede law enforcement’s investigative efforts.
While we have not confirmed that any specific patient, employee, or corporate data was accessed or removed from our network, patients and employees of MMC are encouraged to monitor their personal data for any misuse. Personal data could include names, enrollment information such as group name, identification number, claims or treatment information such as claim numbers, dates of service, procedures, prescription information, dates of birth, email addresses, phone numbers, driver’s license numbers, and, in some cases, social security numbers. Please note that MMC does not store credit card or bank account information within its network.
For over 70 years, MMC has been dedicated to caring for our community. We have faced countless challenges over the years including natural disasters, a world-wide pandemic, and now, a highly sophisticated cyberattack. With your continued support, we will overcome this criminal attack on MMC as we continue our commitment to the health of our community!
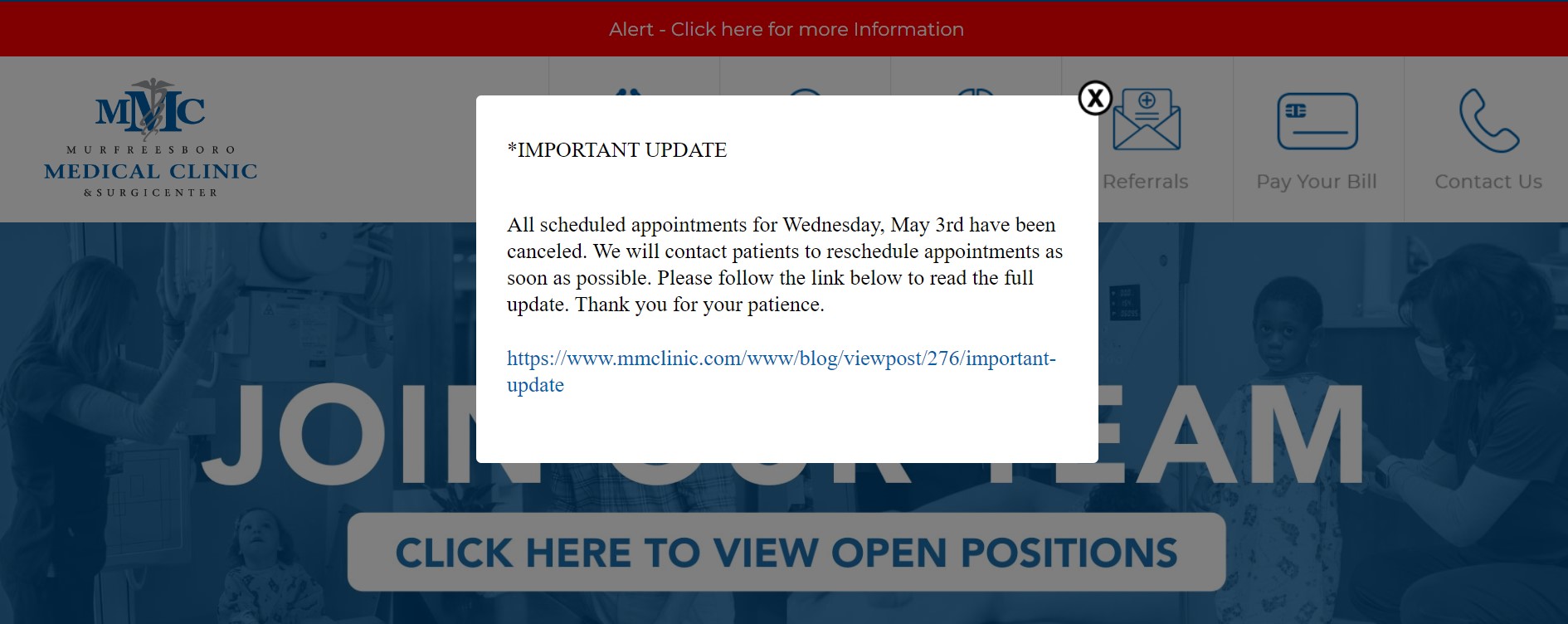
*Please check our website and social media pages for updates regarding hours of operation for Wednesday, May 3rd.