As first reported on DataBreaches on Friday, SingularityMD indicated that they would be leaking or selling Jeffco Public Schools data. They followed through.
In one thread on a popular hacking forum, they leaked what they claim is a 500 MB csv file for an AD Export from November 2020. The leak contains “includes hashed passwords, an effective list of all users and then also servers at the time with local service accounts.”
 Image: DataBreaches.net
Image: DataBreaches.net
In a second thread, they offer, for sale, 90,000 parent email addresses. The listing seeks $1500.00 in XMR or the best offer after 48 hours. They indicate that they will only sell to one buyer.
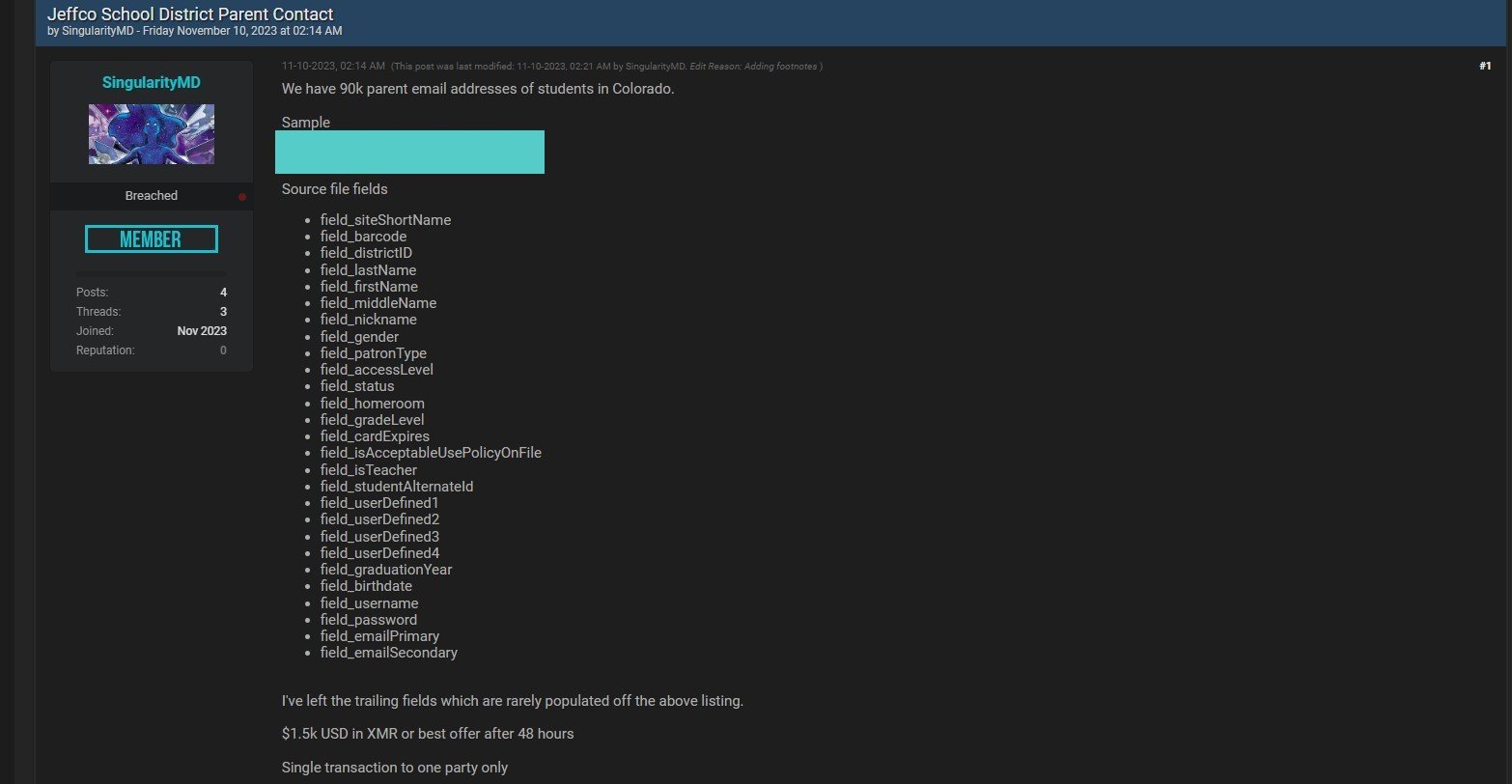 Image: DataBreaches.net
Image: DataBreaches.net
Looking at the time stamp on the parent contacts listing, the 48 hours was actually up at 2:14 am today. The listing did not tell potential buyers how to contact them for purchase and it did not mention accepting escrow. There were no publicly posted replies to the listing or anyone publicly asking how to contact them to make an offer.