CoinPedia reports:
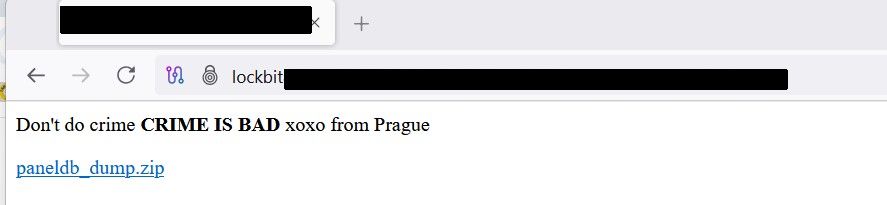
“Don’t do crime. CRIME IS BAD. xoxo from Prague.”
That’s the message left behind after hackers gave LockBit – a ransomware gang known for extorting millions. Yes, they just got a brutal taste of their own medicine. In a surprising breach, nearly 60,000 Bitcoin wallet addresses tied to LockBit’s operations were leaked online.
The attackers broke into LockBit’s dark web affiliate panel and dumped a full MySQL database for the world to see. Inside? Thousands of ransomware builds, private negotiation chats, and crypto wallet addresses used in past attacks.
Read more at CoinPedia.
As also noted by others, the defacement message is the same message we saw on Everest Team’s leak site several weeks ago. DataBreaches is not aware of any group publicly claiming credit for these defacements and hostile actions.
Over on X[.]com, “Rey” from Hellcat posted a screenshot of their Tox chat with LockBitSupp, who confirmed the attack, but downplayed it somewhat.
BleepingComputer provides an analysis of the contents of the SQL dump:
- A ‘btc_addresses‘ table that contains 59,975 unique bitcoin addresses.
- A ‘builds‘ table contains the individual builds created by affiliates for attacks. Table rows contain the public keys, but no private keys, unfortunately. The targeted companies’ names are also listed for some of the builds.
- A ‘builds_configurations‘ table contains the different configurations used for each build, such as which ESXi servers to skip or files to encrypt.
- A ‘chats‘ table is very interesting as it contains 4,442 negotiation messages between the ransomware operation and victims from December 19th to April 29th.
- A ‘users‘ table lists 75 admins and affiliates who had access to the affiliate panel, with Michael Gillespie spotting that passwords were stored in plaintext. Examples of some of the plaintext passwords are ‘Weekendlover69, ‘MovingBricks69420’, and ‘Lockbitproud231’.