From the press release, this appears to be the same ransomware incident that Marin Medical Practices Concepts previously reported. Both MMPC Prima Medical Foundation subsequently reported that 5,000 patients were being notified that patient records were lost during the backup recovery process. Dr. Robinson’s practice appears to have been similarly affected.
On August 22, 2016, Dr. Robinson received confirmed notice from his electronic medical record (EMR) provider that their system was subject to a malware attack on July 26, 2016. The EMR provider became aware of the incident on July 27, 2016, and Dr. Robinson is informed that they promptly secured their systems.
Dr. Robinson immediately requested further information to understand what happened and to determine which patients might be affected. On September 14, 2016, he was provided further detail of the events, and learned that the provider experienced a ransomware infection.
Ransomware is malware that restricts access to the computer system it infects, and demands that a ransom be paid to the malware creator to remove the restriction. A third party forensic IT firm hired to investigate this incident found no evidence that patient information was viewed, transferred or accessed. However, during the restoration process of their system, one of the EMR backup systems caused the loss of consultation notes between July 11, 2016 and July 26, 2016.
The EMR system contains patients’ full name, address, telephone number, date of birth, social security number (if provided to us), medical history, prescriptions, diagnoses, and insurance and health visit information.
If you visited Dr. Robinson between July 11, 2016 and July 26, 2016, those visits’ consultation notes were lost in the EMR recovery process. This information only included what was gathered during the visit: vital signs, clinical history, physical examination notes, and records of the communication between us during the visit. The results of any diagnosis testing were not affected and you do not need re-examination. Importantly, the office is able to recreate the consultation notes from the records restored.
Though there is no evidence that patient information was viewed, transferred nor accessed, given the breadth of information on the system we understand you may want to place a free 90 day fraud alert on your accounts. If so, contact: Equifax (1-888-766-0008; P.O. Box 740241, Atlanta, GA 30374); Experian (1-888-397-3742; P.O. Box 4500, Allen, TX 75013); TransUnion (1-800-680-7289; P.O. Box 2000, Chester, PA 19022-2000). You are also entitled to an annual free credit report at www.annualcreditreport.com.
Protecting your information is incredibly important to Dr. Robinson. If you have any questions, please call toll free number 844-723-9341; or write 619 East Blithedale, Suite A, Mill Valley, CA 94941.
SOURCE: Curtis F. Robinson, M.D., Inc.
I went to the web site to see if the release was posted there or if there was additional information, but encountered this and thought “nope:”
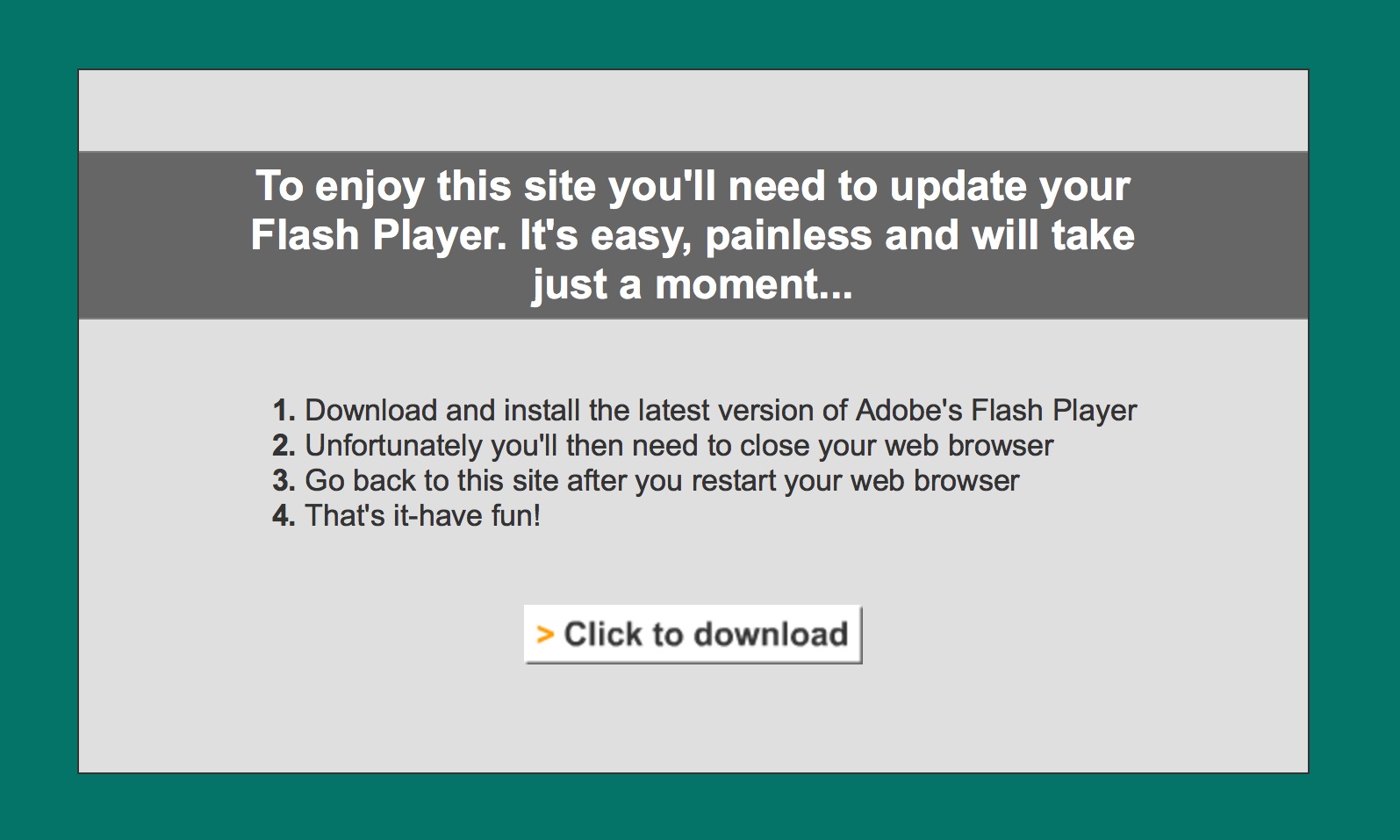
Close call! At least they had a backup to go off of, even though it was old. Better then nothing! Flash Player thing…. ……..