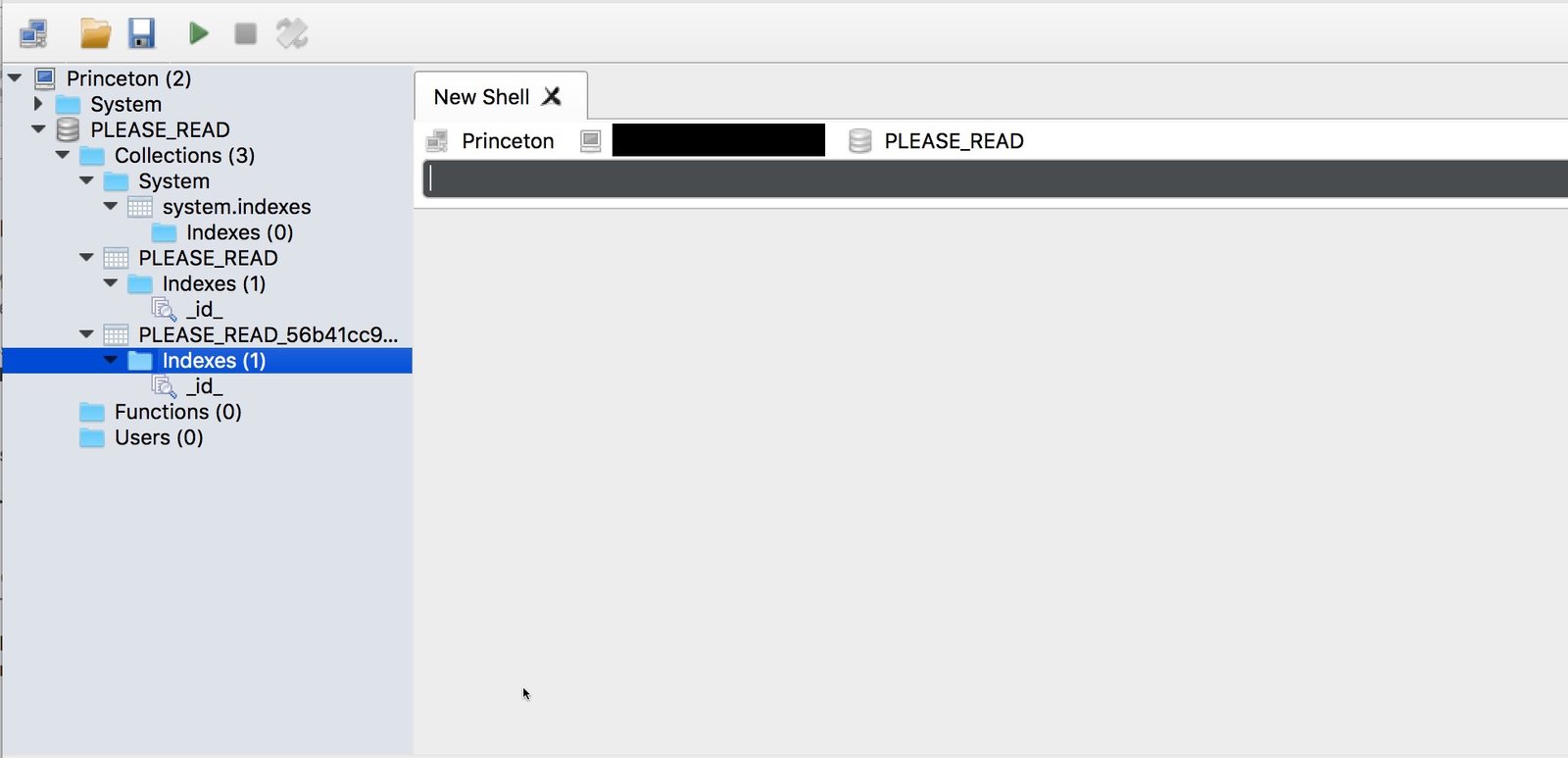
Princeton University became one of the more than 27,000 entities that recently had their databases wiped by attackers who claim that if victims pay ransom, they’ll get their data back. The attackers have been able to access and overwrite databases in MongoDB installations that were left open on Port 27017. With no login or authentication required, anyone can access the files, exfiltrate them, edit them to corrupt the data, or just delete them all. In these cases, the attackers are deleting the databases.
The attack on Princeton was first detected by DataBreaches.net on January 7, and confirmed by Victor Gevers, the ethical hacker and founder of GDI who has been responsible for thousands of notifications.
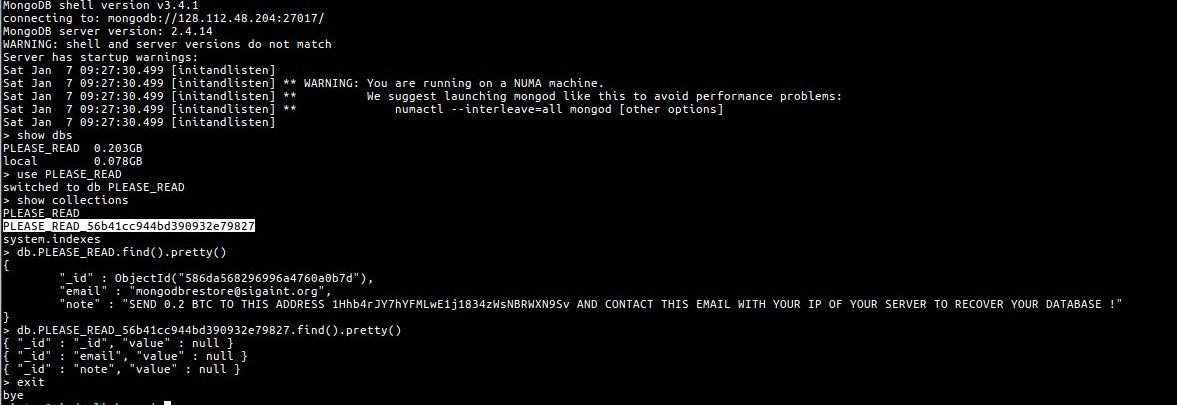
In this case, the replacement database provided an email address of [email protected] and the following note:
SEND 0.2 BTC TO THIS ADDRESS 1Hhb4rJY7hYFMLwE1j1834zWsNBRWXN9Sv AND CONTACT THIS EMAIL WITH YOUR IP OF YOUR SERVER TO RECOVER YOUR DATABASE !
DataBreaches.net sent notification to Princeton immediately and requested a statement from them as to what kinds of data were in the database – specifically, whether it included any student, faculty, or staff personal information.
A spokesperson informed DataBreaches.net today that the university would have no comment on the incident. We don’t know, therefore, whether the data were exfiltrated or just deleted. The second thing we don’t know is whether this was a production database with unencrypted personal information or some other type of database. And third, we do not know whether the database was under Princeton’s direct control or under the control of one of their vendors.
Some transparency seems important here. If you’re a student or faculty member at Princeton, you may want to contact them and ask them for a direct answer as to whether unencrypted personal information was in that database.
And if you find out, please let this site know and we’ll update this post.