Bombas is sending out a breach notification to consumers. It says, in part:
What Happened?
We first started selling Bombas socks online using an outside vendor to develop and manage our website and a third party e-commerce platform for purchases. Malware in the code of the e-commerce platform was identified and initially removed from our website on January 15, 2015, and then finally removed on February 9, 2015.
Given the passage of time, we cannot determine which transactions were impacted. To be safe, we are sending this notice to all of the approximately 41,000 customers who made a credit card purchase on our website during the period the malware may have existed, essentially from the date of launch of our website, September 1, 2013, until the day the identified malware was finally removed. We have subsequently transitioned our website to a different service provider and ultimately a new e-commerce platform.
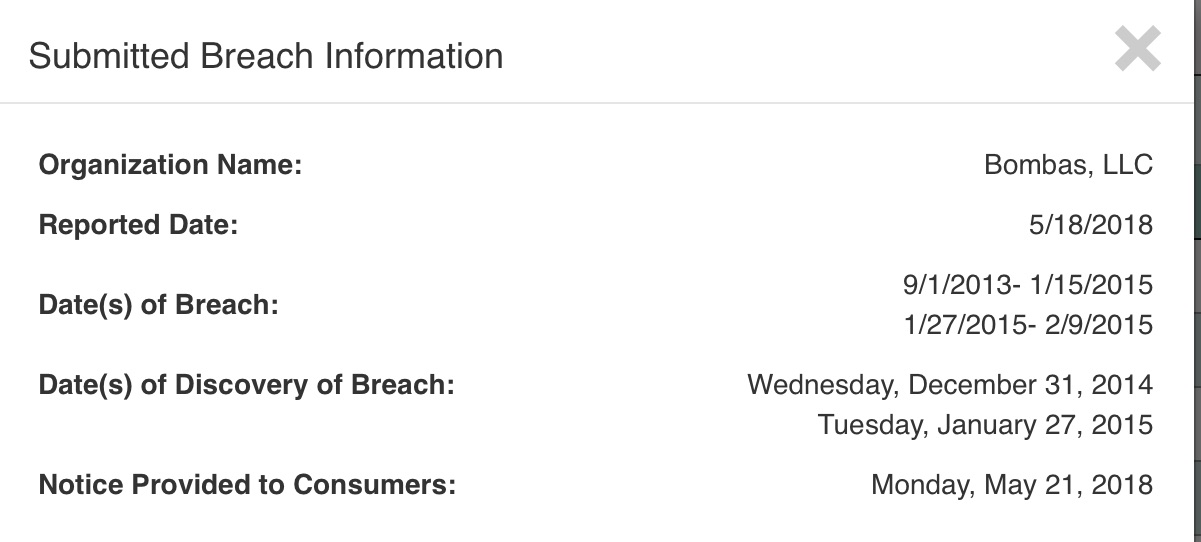
So why did it take from February 2015 until now to send notifications? Here is the time frame as they submitted it to Oregon:
And here is their full notification, as submitted to California:
Bombas Ad r4prf (002)_0DataBreaches.net has sent an inquiry to Bombas asking them to explain the significant gap between discovery and notification, but did not receive an immediate reply. This post may be updated if more information becomes available.