A few weeks ago, DataBreaches.net reported on a leaky Amazon S3 bucket owned by MedCall Advisors in North Carolina. The leak, which exposed approximately 3,000 patients’ protected health information, was discovered by UpGuard, who published a number of redacted screenshots to document the leak. Their detailed report also noted how Randy Baker, the CEO of MedCall Advisors, did not acknowledge or respond to their notification of the leak, although the leak was secured within hours of them sending the CEO an email. MedCall also failed to respond to questions put to it by DataBreaches.net.
 MedCall Advisors not only failed to respond to UpGuard and DataBreaches.net, but, more importantly, perhaps, they never even asked whether we would securely delete any ePHI we may have acquired.
MedCall Advisors not only failed to respond to UpGuard and DataBreaches.net, but, more importantly, perhaps, they never even asked whether we would securely delete any ePHI we may have acquired.
In light of their response – or lack of response – you shouldn’t be totally surprised to learn that a few weeks later, DataBreaches.net was contacted by another researcher, Britton White, who informed this site that MedCall Advisor’s S3 bucket was leaking again.
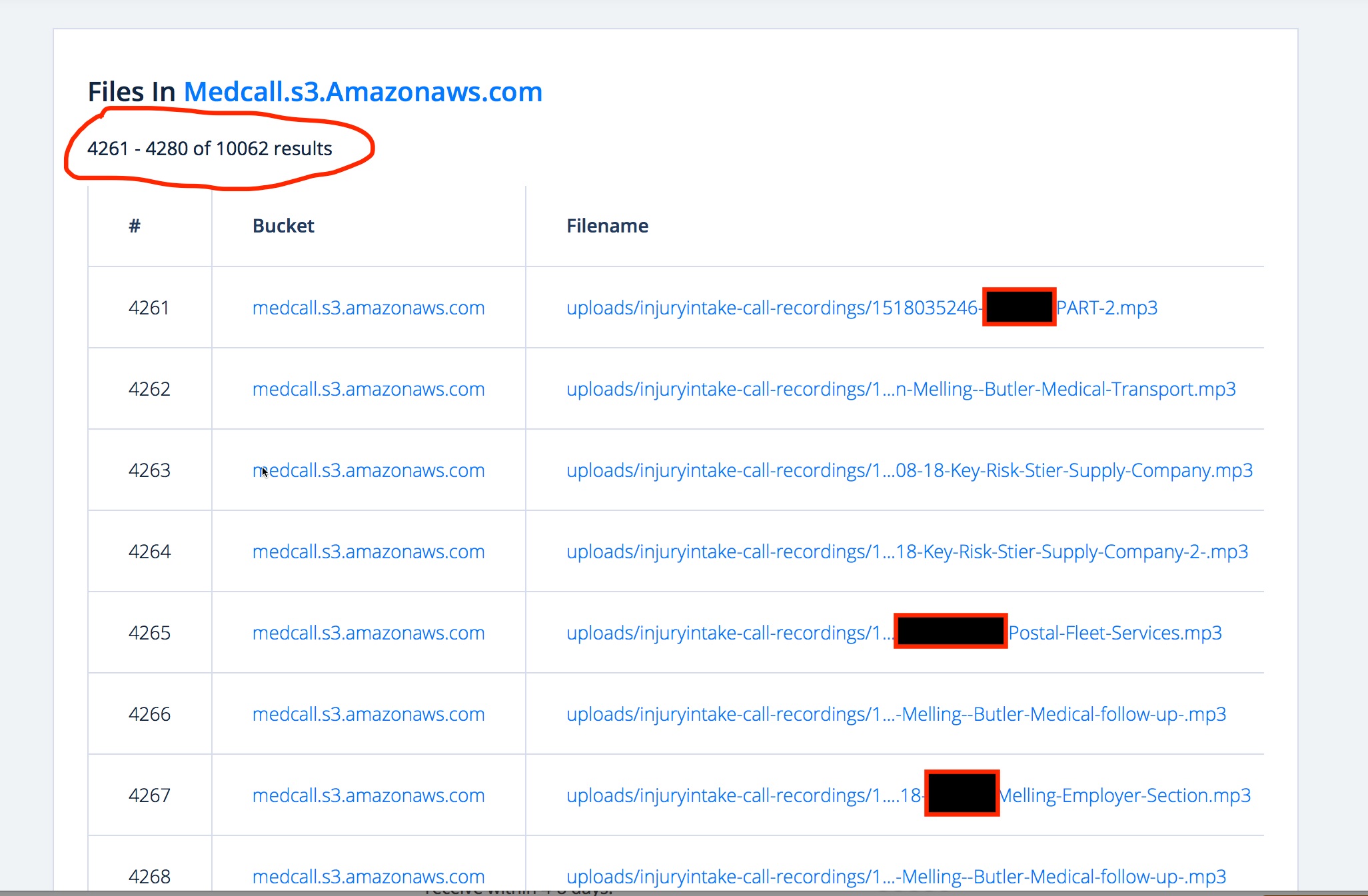
This time, it appeared that 10,000 files might be available for download…. and/or deletion or editing. The leak was noted on grayhatwarefare.com’s site, where any curious soul or criminal could find pages and pages of exposed MedCall files listed for the taking.
White attached a .csv file that included patients’ name, email address, postal address, phone numbers (fixed and cell), gender, date of birth, and Social Security Number.
Other files contained recordings of patient evaluations/conversations with doctors, and records completed by doctors following patient or injured employee contacts. These detailed records contained information such as what medications the patient was already on, any allergies, the nature and detail of their complaint, onset, etc.
Even files that appeared to be deleted from the bucket were actually still available for download. And as before, there were was no login required, no encryption of the data, and the files were writable. DataBreaches.net promptly emailed MedCall Advisors to alert them to this newest leak. Once again, the email notification resulted in security of the data but without any acknowledgement from the firm.
Were any patients, doctors, or client companies notified by MedCall Advisors after the first incident? Are any going to be notified after this second incident?
How many people may have found the exposed files and downloaded them?
All we can say for sure is that there is no report/entry from MedCall Advisors up on HHS’s breach tool at this time, and there is no notice on their web site at this time.
After verifying that the patient names belonged to real individuals, DataBreaches.net sent email inquiries to some doctors whose names appeared in some of the injury contact files to ask if MedCall has notified them of any leak. A few patients and employee supervisors whose names appeared in files were also sent emails asking them whether MedCall Advisors has advised them of any data leak incidents. This post will be updated if any responses are received.
When DataBreaches.net notified Randy Baker of this second leak, this site also asked him how MedCall was going to prevent a third leak. Baker not only failed to acknowledge the courtesy notification that they were leaking patient data, but he did not answer the question as to what steps they would take to prevent a third recurrence.
Maybe they will answer those questions for OCR. Unless, of course, they decide that this is not a reportable breach under HIPAA. But even if they are not covered by HIPAA, they likely have some notifications to make to state attorneys general and patients.
Well I contacted you, Randy
Yes, now you have, and I look forward to being able to update the reporting after we speak.
Some credit would be nice:
Leaks are found at https://buckets.grayhatwarfare.com/
You WERE credited in the figure caption.