Catalin Cimpanu reports:
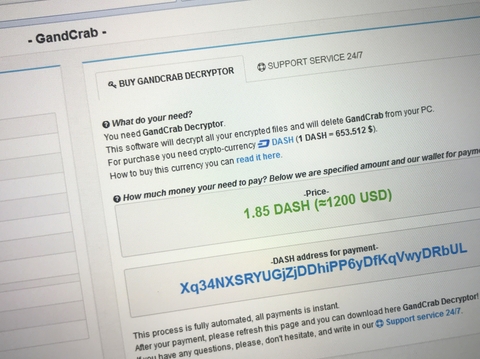
Hackers have used a two-year-old vulnerability in a software package used by remote IT support firms to gain a foothold on vulnerable networks and deploy the GandCrab ransomware on those companies’ customer workstations.
At least one company has been hit already, according to a report on Reddit, confirmed by cyber-security firm Huntress Labs.
The vulnerability used by the hackers impacts the Kaseya plugin for the ConnectWise Manage software, a professional services automation (PSA) product used by IT support firms.
Read more on ZDNet.