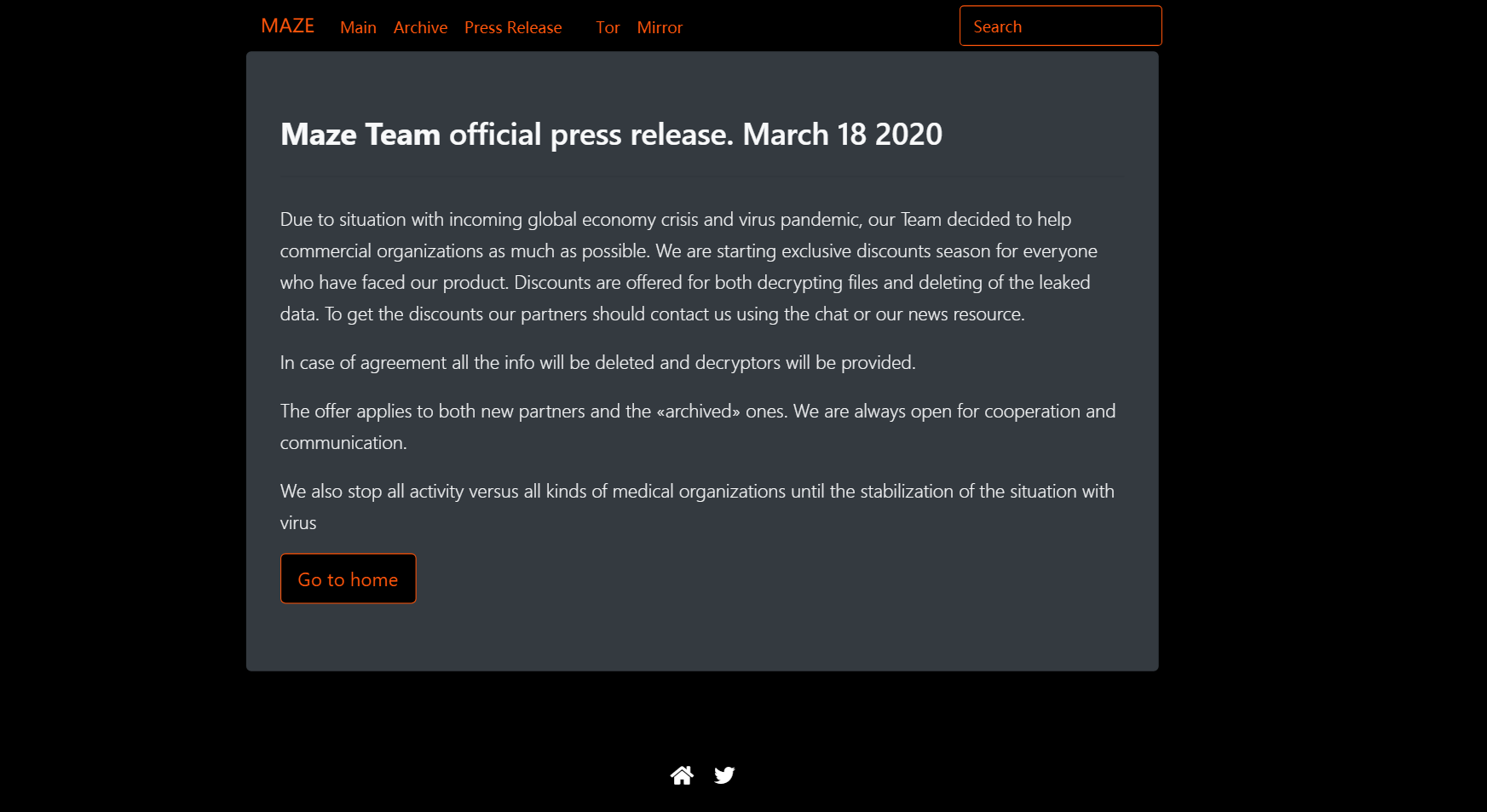
“We’re all in this together” took on new meaning yesterday when a ransomware gang published a statement saying that they were offering their victims (whom they refer to as “partners”) discounts. And in response to an inquiry by Lawrence Abrams of Bleeping Computer, Maze Team also committed to not attacking medical entities during this pandemic crisis, writing, “We also stop all activity versus all kinds of medical organizations until the stabilization of the situation with virus.”
It is not the first time these particular threat actors have made decisions or claims that they frame as being the ethical thing to do. Recently, for example, they had informed DataBreaches.net that they had removed Crossroads Technology’s clients’ data from their website, and had actually assisted some of the hospices by providing free recovery (decryptors) to them.
Blackhats with a heart or ethics? It seems surprising, doesn’t it? But from the beginning, Maze Team had shared some of their thoughts about ethics and morality of what they do. In January, they had responded to an emailed inquiry about how they choose their targets, by writing, in part:
We avoid social objects and we try to avoid large medical centers specializing not just in diagnostics, but in treating patients, so as not to inadvertently cause real physical harm to patients of clinics, therefore the medical topic for us is more an accident than a pattern and deliberate attacks.
So their press release this week is not really inconsistent with what they had said months ago, but it’s still not what you might expect from blackhats who are financially motivated. Contrast their statements with actions by thedarkoverlord who had mercilessly attacked a little nonprofit in Indiana that was helping cancer patients, and who had a member who expressed excitement to me about the thought of possibly driving a vulnerable student to suicide.
So who is Maze Team really, and what drives them? I’d love to know more, but first and foremost, a public thumbs up to them for backing off on medical entities — and presumably any third-party vendors that are critical to medical entities. It may be a small act of kindness in a time of global crisis, but it is an important one.