From the this-doesn’t-bode-well department:
Avaddon threat actors claim to have attacked the City of Dade City, Florida. Although the city has not made any statement either denying or confirming any attack at the time of this posting, the attackers did post some screenshots of directories and files that seem consistent with their claims.
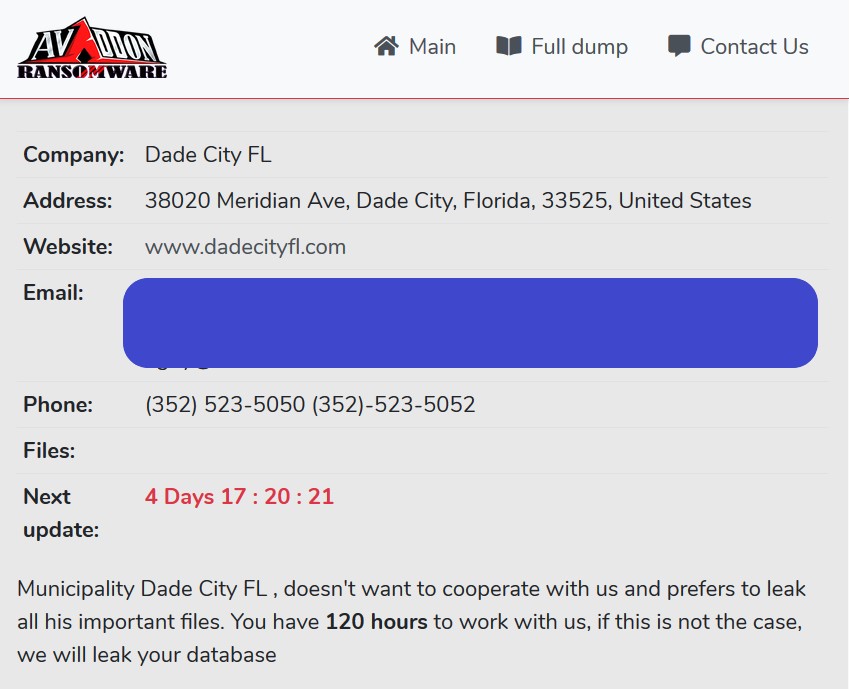
The attackers also threaten to start dumping data in 4+ days if the city does not cooperate.
We appeal to the mayor of the Dade City Camille Sutherland Hernandez If you do not care about the leak, then think about the leakage of personal information of all employees of the police station as well as the municipality, we have many documents that will interest many. Don’t be a bad boss.
More than one of the screenshots does relate to the police department and the filenames suggest that some of the files deal with personnel issues such as complaints, injuries, and other issues that occurred in previous years. A Google search confirmed that at least one of the officers’ names in the list had been a Dade County Police officer at the time of the filestamp.
But even if the attackers acquired old, and potentially embarrassing, files with personnel matters, that doesn’t mean that the city will give in to extortion demands.
As of the time of this posting, DataBreaches.net has received no response to an email sent to the city, but notes that the web site for dadecityfl.com appears to be offline. This post will be updated if a statement is received.
Dec. 22 update: The City of Dade sent this site a copy of their statement of December 8. Other than acknowledging that there was an attack and impact, it doesn’t really add anything new to what we know so far. DataBreaches.net will continue to update this case as updates become available.
July 23, 2021 update: On July 21, external counsel for the City of Dade notified the Maine Attorney General’s Office that 934 people were being notified of this incident. According to their counsel’s notice, the breach occurred on November 22, 2020, and was discovered on June 28, 2021. That discovery date is obviously questionable as they already acknowledged discovery of the breach last year. They seem to be trying to claim that the date they discovered PII was involved is the date of discovery, when discovery should be the date that any reasonable entity would know or have reason to believe that there had been a breach.