This week, a number of universities were added to CLOP threat actors’ dark web leak site. They appear to be linked to the Accellion breach in December and January. As a reminder, many of Accellion’s clients used a standalone server with Accellion’s software to transfer large files. The attack did not hit Accellion’s clients’ own servers or systems, but did enable the threat actors to access whatever was on the transfer server. One of the new additions to CLOP’s site this week was “umd.edu.” This is DataBreaches.net’s report on their incident.
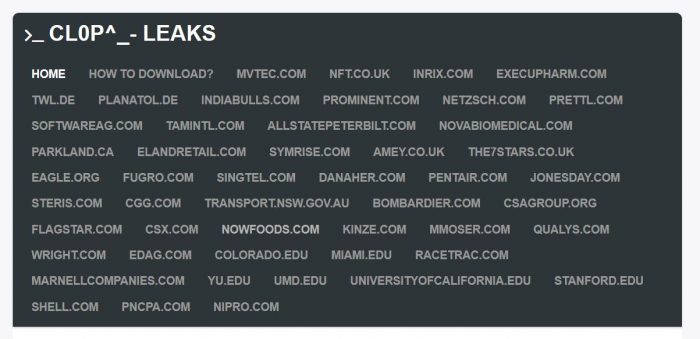
University of Maryland, Baltimore got an unpleasant surprise this week when they saw CLOP threat actors had added “UMD.edu” to their dedicated leak site. The threat actors’ site is used to pressure victims into paying extortion or ransom demands to avoid having data dumped. In the past month or so, CLOP has been adding the names of, and data from, clients of Accellion whose data was stolen by exploting vulnerabilities in Accellion’s older standalone file transfer system.
DataBreaches.net reached out to UMD earlier this week, only to learn that it wasn’t the College Park campus that had been the victim. It was UMB (University of Maryland, Baltimore) who was impacted. Alex Likowski kindly provided this site with a statement on behalf of UMB:
In late December, CLOP breached the security of our Accellion file transfer system. This system was used by our students, faculty, and staff to transfer encrypted files. We discovered the breach earlier this week, when the hackers posted evidence that they had accessed a limited number of files in our system containing some personally identifiable information.
In a follow-up communication, Likowski confirmed that UMB’s Center for Information Technology Service team had discovered the listing because they were monitoring certain sites where such information would be posted. “Neither UMB nor Accellion were aware of the breach until this week,” he informed DataBreaches.net.
There is no evidence that the file transfer system was compromised at any other time up to the date it was decommissioned and replaced in February.
Importantly, the statement also noted that UMB’s investigation showed that “every appropriate security measure was taken by our Center for Information Technology Services, including rigorous monitoring and the timely installation of all patches and upgrades provided by Accellion.”
UMB has reached out to the owners of the compromised files and offered them security assistance, including free credit monitoring and identity restoration services. UMB has also informed federal and state authorities of this incident.
Yesterday, the threat actors began dumping files. DataBreaches.net has not yet acquired nor examined those files, but when asked how many people had to be notified of the breach, Likowski responded:
So far we’ve only had to notify a very small number of users. We will continue to monitor of course, and hope for the best.
Amen to that.