Admire Moyo reports:
The Nama Khoi Municipality in the Northern Cape Province is struggling to restore IT systems that were hit by a ransomware attack last year.
This was revealed by the municipality’s chief information officer, Brandon Love, in an e-mail interview with ITWeb.
According to Love, on Wednesday, 9 December 2020, the municipality’s ICT systems were compromised by a ransomware virus infection.
Read more on ITWeb. What’s a bit bizarre about this report is that they report that the Pysa threat actors have not even yet demanded any ransom. DataBreaches.net checked the threat actors’ leak site. They listed the attack as occurring on November 29, 2020. And then they started dumping data as proof.
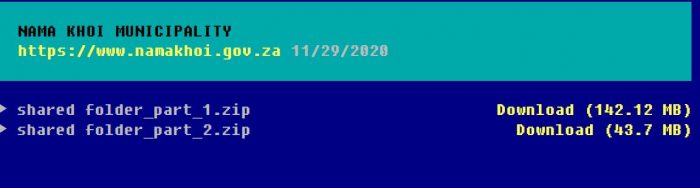
DataBreaches.net examined some of the files in the data dump. They appeared to be mostly the type of files that you would find as public records.
But why did the threat actors dump any data but not make any ransom demand? That makes no sense. Normally threat actors post a few screencaps as proof of claims. But they do not dump data like this unless their victim was refusing to pay ransom or ignoring their demands. So what happened here? Did they issue a demand that Nama Khoi did not see? Or did Pysa somehow screw up?
Pysa is not usually very quick to follow up, so it may be a while before we find out more about this one.